Malware that can evade security measures, like air-gapped environments, is becoming a bigger threat in the rapidly changing field of cybersecurity This article explores cryptojacking type cyberattack. . Crypto-mining malware, which propagates through external drives and takes advantage of flaws in systems that appear to be secure, is one of the most advanced threats that have been discovered recently.
In addition to demonstrating the tenacity of contemporary malware, this campaign demonstrates the ingenious strategies employed to endure and spread within extremely secure settings. Cryptojacking, a type of cyberattack in which malware takes over a system's resources to mine cryptocurrency, has developed from straightforward browser-based scripts to intricate, system-level dangers. The most recently found malware employs a variety of sophisticated strategies, including kernel exploitation and worm-like propagation, to take over system resources and continuously make money for the attackers without warning users.
Cryptojacking is a persistent and ongoing threat because, in contrast to traditional ransomware, it generates passive revenue. The malware can infiltrate a number of systems, including "air-gapped" systems—systems that are not connected to the internet. Usually, these isolated systems are employed in settings like critical infrastructure or research where security is crucial.
Look for a particular date logic (Source: trellix). However, this malware easily gets around the isolation by using external drives, USB sticks, hard drives, or other removable media as its main propagation method. The Mechanisms of Infection and Propagation A social engineering attack is how the malware starts its journey. Attackers frequently pose as trustworthy tools, like productivity apps, and distribute compromised software included in pirated software.
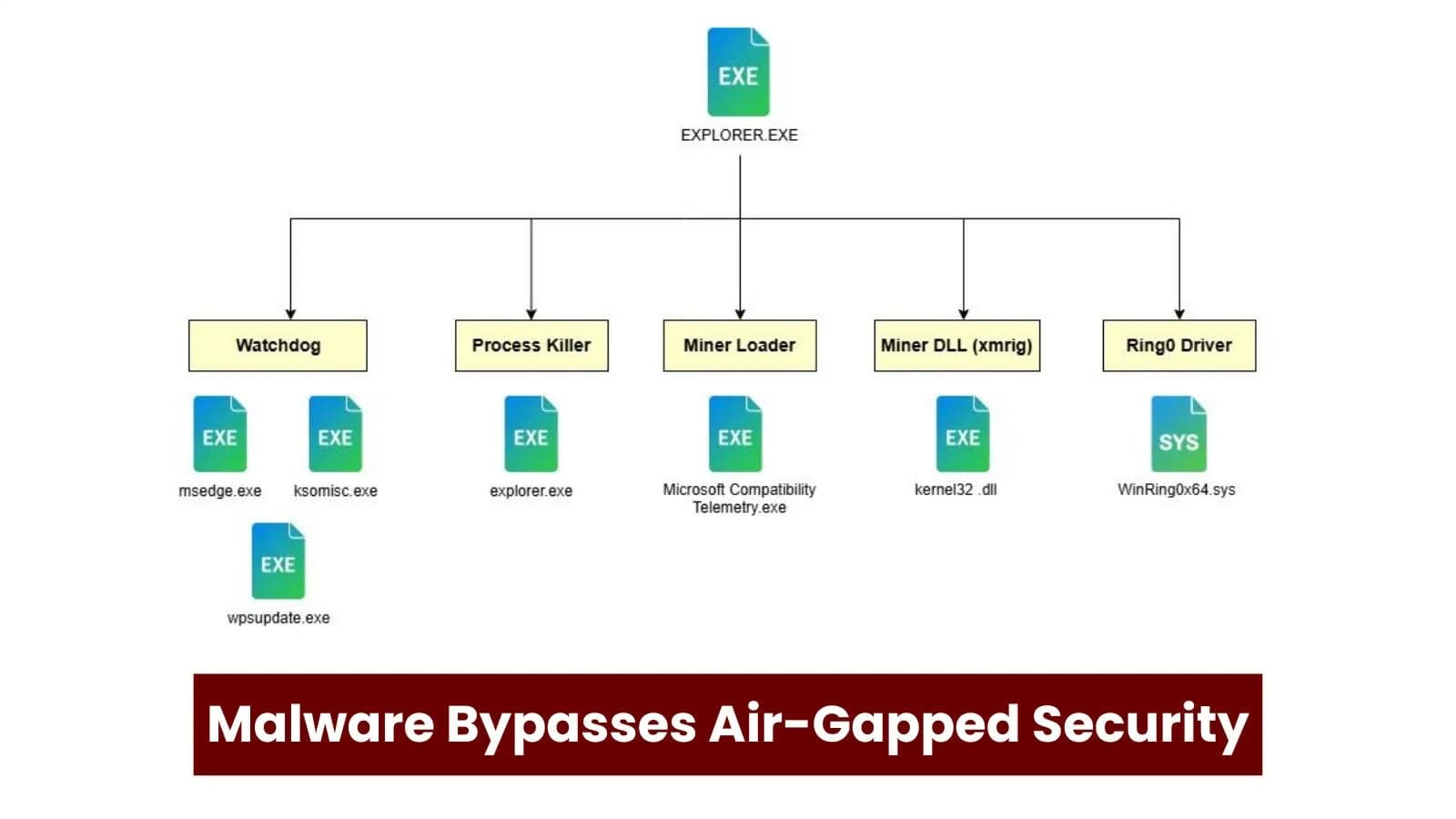
The malware starts running on the computer as soon as the user installs the program, dropping several payloads that combine to cause a persistent infection. "Explorer.exe," the main controller of the infection, is one of the main parts of this malware. From the initial installation to sustaining persistence on the compromised system, it orchestrates the various phases of the attack.
Some of the malware's components pose as genuine Windows processes in order to evade detection and guarantee longevity. Getting Around Air-Gapped Systems This malware's ability to get around air-gapped systems makes it special. Air-gapped systems are frequently regarded as extremely secure since they are cut off from outside networks to avoid data breaches.
Nevertheless, this malware deftly takes advantage of the reliable connection between external devices and internal systems by using external drives as a bridge. The barusu flag is handled by the else block (Source: Trellix). The malware spreads to other systems after it is run on an external drive, getting around the isolation that is supposed to shield them.
Meaning of a Code Artifact WM_DEVICECHANGE (537) keeps track of hardware modifications. DBT_DEVICEARRIVAL (0x8000) detects a device that is plugged in. DBT_DEVTYP_VOLUME (2) Verifies the amount of storage. Drive letters 65–90 scan from E: to Z:.
sub_140014190 copies payload to drive. This sophisticated malware campaign shows that air-gapped systems are not impervious to contemporary cyberthreats. The attack shows how advanced malware can leverage external devices to bypass even the most sophisticated security measures.
Stronger safeguards for external devices must be put in place by organizations, and even isolated systems must be constantly watched for possible dangers. To counter these increasingly complex attacks, regular updates and employee awareness training are crucial, particularly with regard to the dangers of pirated software. According to Trellix, this campaign is a reminder that without proactive, multi-layered defenses, no cybersecurity system is completely safe from changing threats.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)