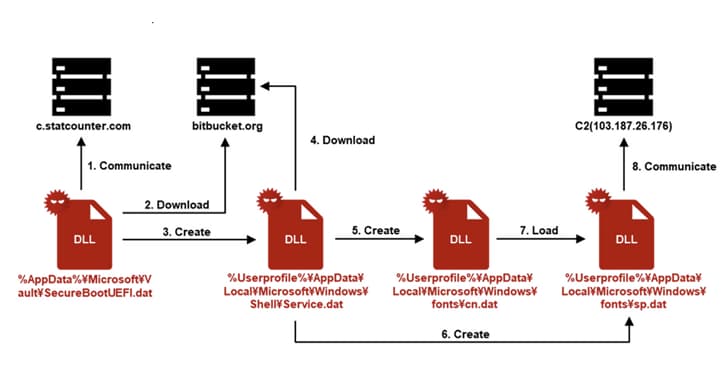
According to JPCERT/CC, APT-C-60 delivered the SpyGlace backdoor using a lure with a job application theme. The attack made use of trustworthy services like Bitbucket, Google Drive, and StatCounter. Around August 2024, an unidentified Japanese organization was the target of the attack.
In order to steal files, load more plugins, and carry out commands, the backdoor, on the other hand, connects to a command-and-control server and waits for additional instructions. "Groups from the Asia region continue to use non-standard techniques to deliver their malware to victims' devices," according to Positive Technologies. According to independent reports from Chuangyu 404 Lab and Positive Technologies, "one of these techniques is the use of virtual disks in VHD/VHDX format to bypass the operating system's protective mechanisms," the spyGlace malware was distributed through similar campaigns. Evidence suggests that APT/Q-12 and Pseudo Hunter are subgroups of the DarkHotel cluster, which is noteworthy.
Japan, South Korea, China, and the United States are among the East Asian nations that the groups are known to target. The threat actor behind the attack is believed to be based in South Korea and has been linked to a South Korean cyber espionage group known as the "DarkHotel" group, according to the JPCERT-CC report.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)