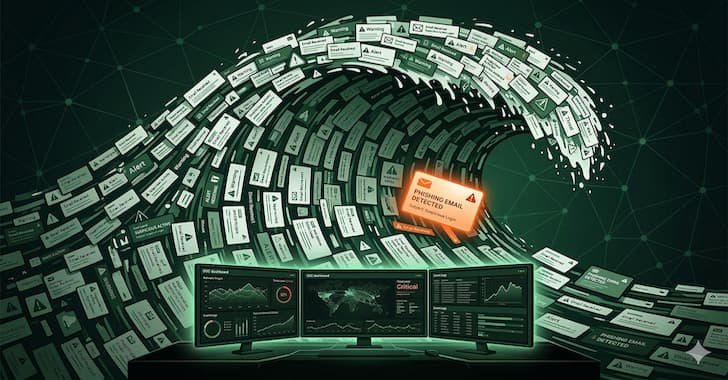
The most dangerous phishing campaigns don't just try to trick employees. Many of them are made to wear out the people who are looking into them. If a phishing investigation takes 12 hours instead of five minutes, the situation can go from a contained incident to a breach.
For years, the cybersecurity industry has focused on the front door of phishing defense: employee training, email gateways that filter known threats, and reporting programs that encourage users to flag suspicious messages. There hasn't been as much focus on what happens after a report is made and how attackers take advantage of the investigation that follows. ## The Economics of the Attack The economics of this situation strongly favor the attacker.
Creating thousands of phishing emails for goods is cheap, especially now that generative AI has made it even easier to do. But every time an employee reports one of those emails, it costs the defending organization real analyst time and mental bandwidth. This makes things uneven, and traditional SOC models don't have a good answer for this: Cost for the attacker to send a decoy email: almost nothing.
Template-based generation, basic infrastructure, and automated delivery. Security teams are right to be wary of "black box" automation that makes decisions without showing how it got there. When an automated system closes a phishing report and no one can say why, trust goes down. Analysts second-guess the automation, look into cases it has already handled again, or automatically go against its decisions.
The efficiency gains go away, and the company ends up with the worst of both worlds: it has to pay for automation and can't stop doing things by hand. More importantly, static rules can't change to fit the changing relationship between attack patterns and SOC behavior. The human analysts, the skilled professionals that every SOC needs, go from processing queues reactively to doing the work that really needs human judgment: looking into confirmed incidents, looking for threats that haven't set off alerts, and making strategic decisions about how to defend.
How to Measure SOC Resilience Companies that use this framing need metrics that show it. Mean time to acknowledge, mean time to close, and tickets processed per analyst are all examples of traditional SOC metrics that measure how well an organization runs. They don't check to see how resilient something is against being used by an enemy.
Metrics that measure how well a defense can handle weaponized volume include: The quality of the investigation stays the same under load.