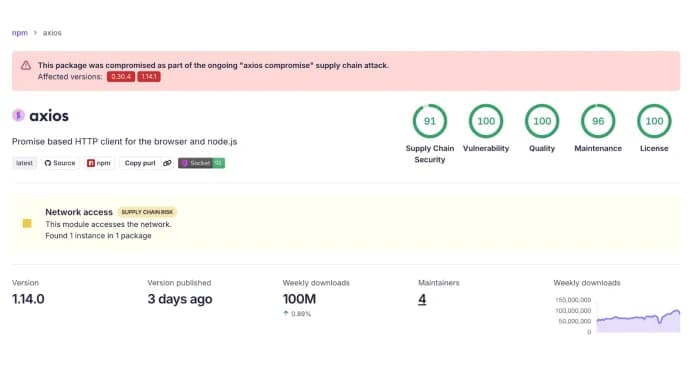
Axios, one of the most popular HTTP clients in the JavaScript ecosystem, has been hit by a complicated supply chain attack This article explores hacked versions axios. . The breach includes the unauthorized release of new Axios versions that automatically download plain-crypto-js@4.2.1.
The potential blast radius of this supply chain poisoning is very large because Axios is used in so many modern web development projects. Security teams, DevOps engineers, and developers need to quickly check their software supply chains to find and get rid of the parts that have been hacked. The registry published the malicious payload dependency on March 30, 2026, at 23:59:12 UTC. The hacked versions of Axios went live just minutes after this article was published.
If any of these specific package versions are found in your environment, you must either completely remove them or roll back your dependencies to a known safe release, like Axios 1.14.0, to stop the injected code from running. This is still an active and quickly changing security incident, so we need to keep looking for threats and keep an eye on things to find out how bad the breach is and stop it from happening again. The fact that this account is in the compromised dependency chain raises serious questions about the ability to publish packages without permission.
It suggests that the attackers may have taken over an account, gotten hold of developer credentials, or stolen a session token that let them log in and publish the harmful files directly to the npm registry.
This method lets threat actors run any code they want through transitive dependencies without drawing attention to themselves, which usually happens when big changes are made to codebases or logic. Making small, specific changes is a common and very effective way to attack a supply chain. The only change was adding the bad plain-crypto-JS package to the dependency tree.
The attack was meant to spread as much as possible before security tools could do anything. The attackers made only small changes to the main Axios codebase to avoid being found right away during the first phase of the infection.