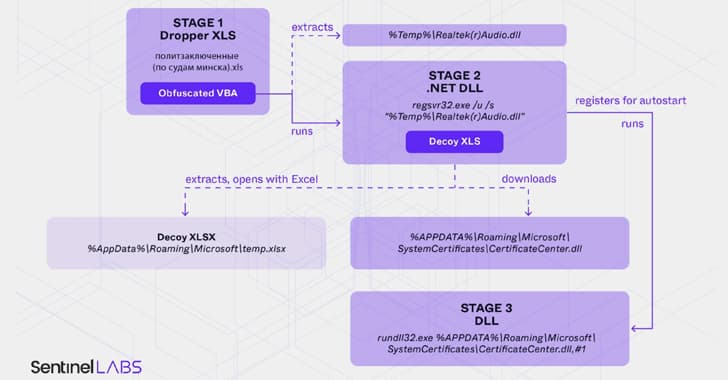
It has been determined that the threat cluster is an extension of an ongoing campaign carried out by a threat actor with ties to Belarus. An obfuscated macro is executed when a malicious Excel workbook included in the RAT file is opened. The victim is shown a fake Excel file in the following stage while more payloads are downloaded to the system in the background.
The Cobalt Strike post-exploitation framework was delivered using this method as recently as June
2024.
According to SentinelOne, it also found additional weaponized Excel documents with lures with a Ukrainian theme that used a technique called steganography to retrieve an unidentified second-stage malware from a remote URL ("sciencealert[. ]shop") in the form of a seemingly innocuous JPG image. The URLs are no longer accessible. According to SentinelOne, "cyber threat actors associated with Belarus appear to have no reservations about conducting cyber espionage operations against Ukrainian targets, even though Belarus does not actively participate in military campaigns in the war in Ukraine."











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)