A suspected state-sponsored cyber espionage operation based in China has been going after military groups in Southeast Asia since at least 2020. Palo Alto Networks Unit 42 is keeping an eye on the threat activity known as CL-STA-1087, where CL stands for cluster and STA stands for state-backed motivation. Security researchers Lior Rochberger and Yoav Zemah said, "The activity showed strategic operational patience and a focus on highly targeted intelligence collection, rather than bulk data theft."
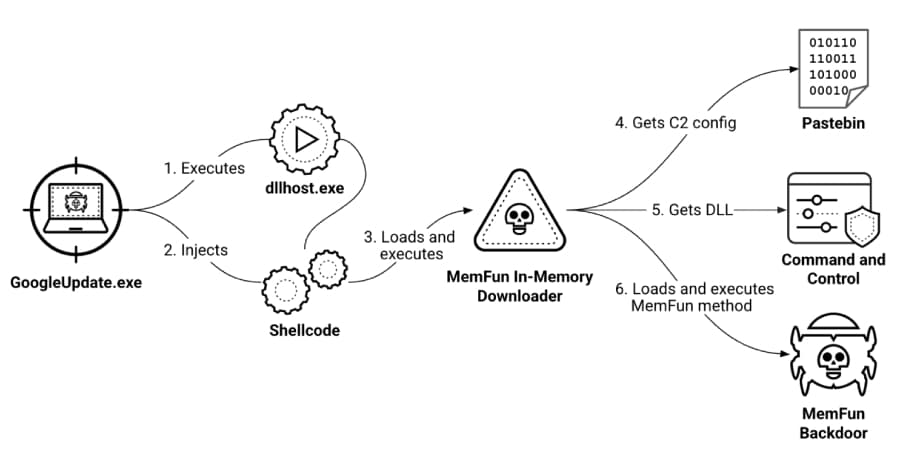
"The attackers behind this cluster actively searched for and gathered very specific files about military capabilities, organizational structures, and working together with Western armed forces."" The campaign has many of the same traits as advanced persistent threat (APT) operations, such as carefully planned delivery methods, strategies for avoiding detection, a very stable operational infrastructure, and custom payload deployment that allows for long-term unauthorized access to compromised systems. The threat actor used backdoors called AppleChris and MemFun and a credential harvester called Getpass to do bad things.The threat actor behind the cluster demonstrated operational patience and security awareness," Unit 42 concluded.
"They maintained dormant access for months while focusing on precision intelligence collection and implementing robust operational security measures to ensure campaign longevity."