Evasive Panda, a threat actor with ties to China, targeted a government agency and a religious group in Taiwan. They were infected by the threat actor using a post-compromise toolset known as CloudScout that was not previously documented. According to the Slovak cybersecurity firm, the use of the.NET-based malware tool was discovered between May 2022 and February
2023.
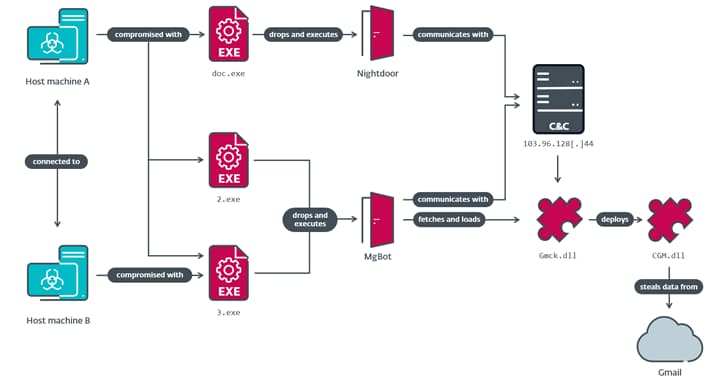
It includes ten distinct C# modules, three of which are designed to steal data from Google Drive, Gmail, and Outlook. Each of these modules is implemented by a C++-programmed MgBot plugin. The development coincides with the Canadian government's accusation that a "sophisticated state-sponsored threat actor" from China was conducting extensive reconnaissance operations against multiple Canadian domains over a period of several months.
Numerous organizations were also targeted, including media outlets, think tanks, NGOs, democratic institutions, critical infrastructure, and the defense industry. According to a statement, "the majority of affected organizations targeted were government of Canada departments and agencies, and includes federal political parties, the House of Commons, and Senate." The group is also well-known for planning supply chain and watering hole attacks against the Tibetan diaspora in Hong Kong and Taiwan. The remaining modules' purpose is still unknown.
For later exfiltration by either Mg Bot or Nightdoor, the data collected by the three modules—mail folder listings, email messages (including attachments), and files with specific extensions—is compressed into a ZIP archive. Nevertheless, cookie-theft malware will eventually become outdated due to Google's new security measures, like Device Bound Session Credentials (DBSC) and App-Bound Encryption. By stealing cookies and using them to obtain unauthorized access, the modules are intended to take over authenticated browser sessions.