Cybersecurity researchers have revealed information about a new campaign that uses a signed Microsoft Application Virtualization (App-V) script and ClickFix-style fake CAPTCHAs to spread Amatera, an information stealer This article explores powershell directly attacker. . In a report released last week, Blackpoint researchers Jack Patrick and Sam Decker stated, "Instead of launching PowerShell directly, the attacker uses this script to control how execution begins and to avoid more common, easily recognized execution paths."
In order to hide the malicious activity, the App-V script will be converted into a living-off-the-land (LotL) binary that uses a trusted Microsoft component to proxy the execution of PowerShell.
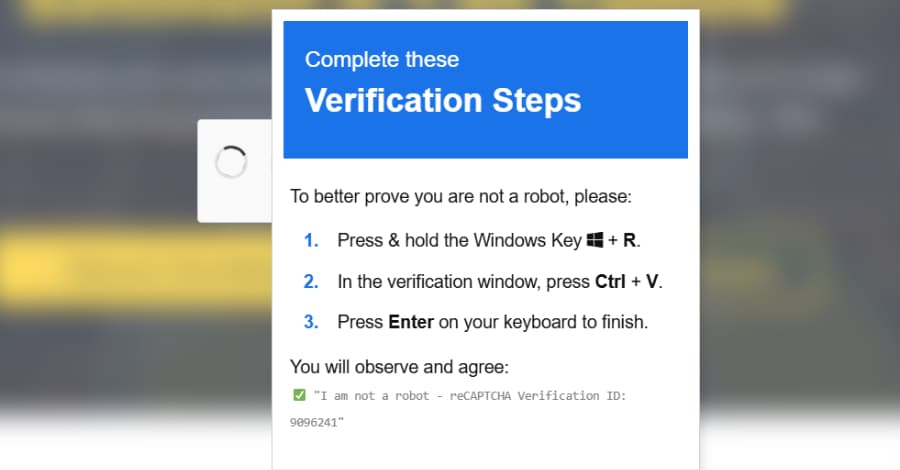
The attack begins with a phony CAPTCHA verification prompt that aims to fool users into pasting and running a malicious command on the Windows Run dialog. This is where the attack differs from conventional ClickFix attacks, though.
"From requiring manual user interaction to validating clipboard state to pulling live configuration from a trusted third-party service, each step reinforces the previous one." "The outcome is an execution flow that only advances when it unfolds (almost) exactly as the attacker expects, which makes both automated detonation and casual analysis significantly harder." ### ClickFix's Development: JackFix, CrashFix, and GlitchFix The disclosure comes as ClickFix has become one of the most widely used initial access methods in the last year, accounting for 47% of the attacks observed by Microsoft.
Social media content creators have been the target of recent ClickFix campaigns that claim they are eligible for free verified badges and instruct them through videos to copy authentication tokens from their browser cookies into a fictitious form in order to finish the purported verification process. Additionally, the embedded video advises the user to "not log out for at least 24 hours" in order to maintain the validity of the authentication tokens. According to Hunt.io, the campaign, which has been active since at least September 2025, is thought to have used eight exfiltration endpoints and 115 web pages throughout the attack chain.
In order to facilitate account takeover after token theft, the activity primarily targets creators, monetized pages, and companies looking for verification.
The ClickFix command copied to the clipboard exploits "SyncAppvPublishingServer.vbs" to obtain the final payload hosted on the jsDelivr content delivery network (CDN), just like in the Amatera Stealer attack. Up to 147,521 systems have probably been compromised since late August 2025, according to Expel's analysis of the ClearFake campaign. Marcus Hutchins, a security researcher, stated that "whether said behavior is being performed by a trusted application is one of many factors security products use to decide if behavior is malicious or not."
"In this instance, 'SyncAppvPublishingServer.vbs' is a default Windows component, and only TrustedInstaller—a highly privileged system account used internally by the operating system—can alter the file.
As a result, the file and its actions by themselves wouldn't typically raise red flags. Since it would prevent the component from being used for its intended purpose, organizations and EDR are unlikely to completely prevent SyncAppvPublishingServer.vbs from starting PowerShell in hidden mode.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)