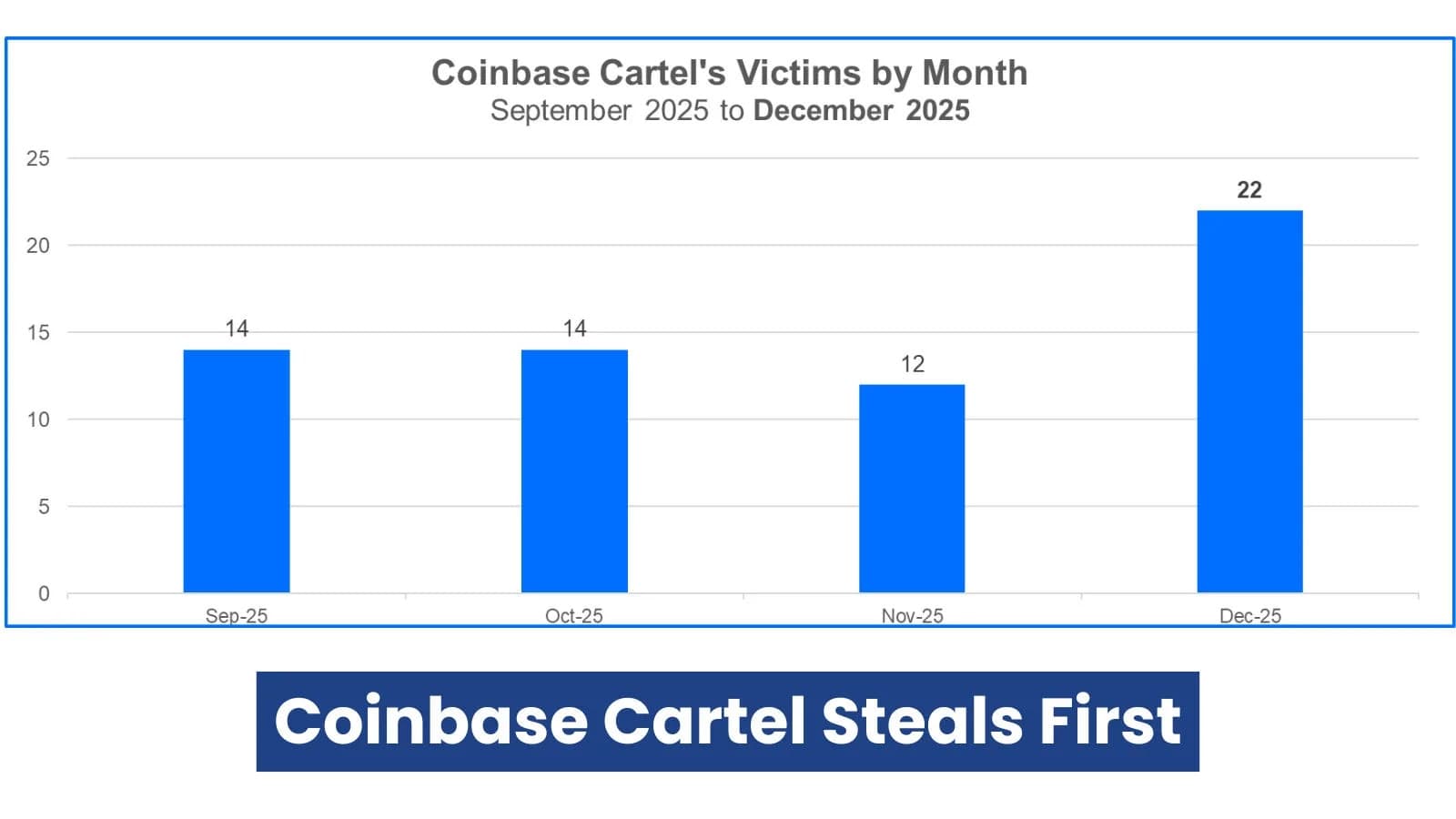
In September 2025, Coinbase Cartel, a ransomware group, made its debut and claimed 14 victims in that month alone This article explores coinbase cartel ransomware. . With more than 60 victims in its first few months, it was listed among Bitdefender's Top 10 ransomware groups by December.
This type of ransomware steals data first and bypasses encryption, in contrast to traditional ransomware that locks up files. This "data exfiltration" method is quicker and more silent. Victims must decide between paying to keep secrets private and letting them leak online. According to Bitdefender's reports on the evolution of ransomware, it's a part of a larger trend.
Victim Demographics and Operations The Coinbase Cartel avoids noisy encryption by stealing data while leaving systems operational. This raises concerns regarding their objectives and potential connections to other hackers.
They target high-profit industries and stage leaks on dark websites, just like many other groups. Small businesses with millions of dollars in revenue and large corporations with hundreds of billions are among the victims. More than half of their 2025 goals are in the areas of healthcare, technology, and transportation.
Notably, they raised a red flag by targeting ten healthcare groups in the United Arab Emirates in a single month. Identity theft and damage to one's reputation are fueled by sensitive patient information (PII and PHI) in the healthcare industry. Is the UAE economy being targeted geopolitically, or is this just pure profit? The group sneaks in, modifies logs, and steals data using admin tools, social engineering, and broker credentials that have been stolen.
First, the Coinbase Cartel Steals (Source: bitdefender) Following the release of the data, they demand Bitcoin ransoms and list the names of the victims on their leak website.
Following a 48-hour chat period, victims have 10 days to make payment or engage in negotiations. Partnerships and the Data Leak Site Among the pages on their website are HOME (which displays victim statuses such as active, leaking, and leaked), AUCTIONS (which are currently empty), PARTNERSHIPS, and CONTACTS. They claim to be "redefining data extortion," which is bold but not revolutionary.
According to Bitdefender's analysis of AI-centric groups, others, such as FunkSec, have also put data up for auction. Coinbase Cartel Data Leak Site's auctions page (Source: bitdefender) Instead of using the Ransomware-as-a-Service (RaaS) model, they operate independently, selling stolen data and looking for partners. They paid more than $2 million for zero-day exploits last fall. Rumors link them to ShinyHunters, but the proof is thin.
Partnerships with flexible agreements like revenue shares or fixed pay require proof of hacks.
According to Bitdefender's DragonForce report, there is no proof that they bullied competitors like DragonForce did, so don't call them a real "cartel." Coinbase Cartel outperforms another data-only group, PEAR (Pure Extraction and Ransom), in several ways, including more victims per month (17 vs. 13), a broader range of industries, and greater attacks on the tech and healthcare sectors. They remain sly with few OPSEC slips into 2026.
Requirements for Coinbase Cartel partnership submissions (Source: bitdefender) Take these precautions to keep yourself safe: Apply least privilege and enforce MFA everywhere, especially for admin accounts. Quick fixes for unresolved software bugs are easy doors. Make frequent backups, test restores, and store offsite (on external drives or the cloud). Keep track of sensitive data's location, who can access it, and lock it down.
For TTP awareness, use threat intelligence. Use MDR services, such as Bitdefender's, to ensure prompt detection and response. Utilize tools such as GravityZone PHASR, which detects living-off-the-land tactics in the majority of high-severity attacks, to reduce the size of your attack surface.
Bitdefender uses monthly Threat Debriefs to monitor the Coinbase Cartel and the ransomware landscape. Data theft is the new silent killer, so be on the lookout.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)