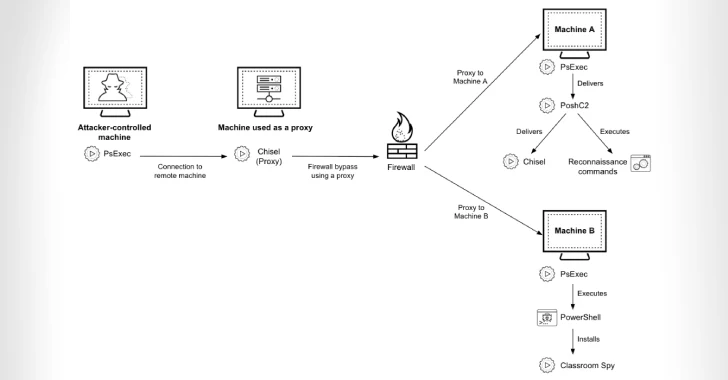
Since at least July 2023, financial institutions throughout Africa have been the target of several cyberattacks, which cybersecurity researchers are drawing attention to. The activity is being monitored by Palo Alto Networks Unit 42 under the code CL-CRI-1014, where "CL" stands for "cluster" and "CRI" for "criminal motivation." The use of programs like Classroom Spy for remote administration, Chisel for tunneling malicious network traffic, and PoshC2 for command-and-control (C2) are characteristics of the attacks. The revelation coincides with the discovery by Trustwave SpiderLabs of a new ransomware group known as Dire Wolf, which since its appearance last month has already claimed 16 victims in the United States, Thailand, Taiwan, Australia, Bahrain, Canada, India, Italy, Peru, and Singapore.
Financial services, manufacturing, and technology are the most heavily targeted industries. Threat actors are said to have stolen user credentials and used them to set up a proxy using Posh C2, though it's unclear exactly how they breach target networks.In a blog post on Monday, the cybersecurity firm stated, "Organizations should follow good security practices and enable monitoring for the techniques revealed in this analysis, even though no initial access, reconnaissance, or lateral movement techniques used by Dire Wolf are known at this time." According to researchers Tom Fakterman and Guy Levi, "the threat actor forges file signatures by copying signatures from legitimate applications, disguising their toolkit and masking their malicious activities." A spear-phishing campaign known as DangerousSavanna, which targeted financial and insurance firms in Ivory Coast, Morocco, Cameroon, Senegal, and Togo, was described by Check Point in September
2022.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)