A threat actor operating in Pakistan has used previously unreported tradecraft to target Indian government entities in two campaigns This article explores iso file malicious. . Zscaler ThreatLabz discovered the campaigns in September 2025 and codenamed them Gopher Strike and Sheet Attack.
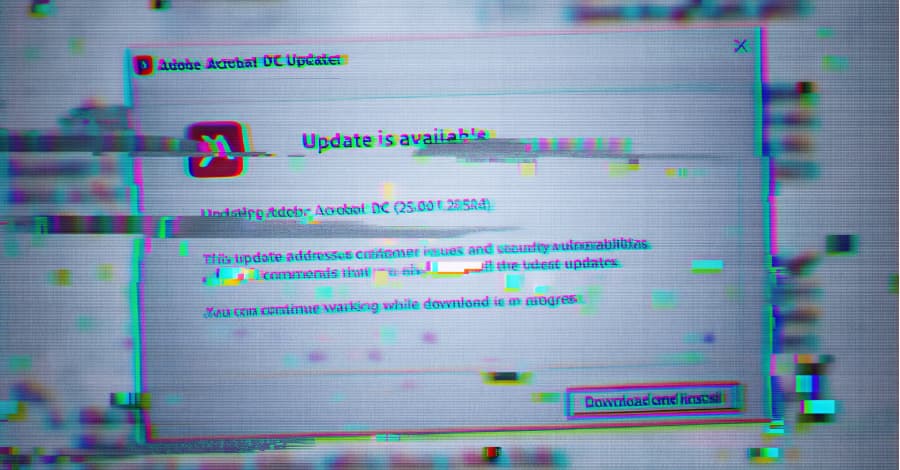
The use of reputable services like Google Sheets, Firebase, and email for command-and-control (C2) is how Sheet Attack got its name. However, it is determined that Gopher Strike used phishing emails as a springboard to send PDF documents with a blurry image overlaid by a seemingly innocuous pop-up telling the recipient to download an Adobe Acrobat Reader DC update.
The image's primary goal is to convey to users that installing the update is required in order to access the contents of the document. Only when the requests come from IP addresses in India and the User-Agent string matches Windows does clicking the "Download and Install" button in the fictitious update dialog cause an ISO image file to be downloaded. According to Zscaler, "these server-side checks ensure that the malicious file is only delivered to intended targets by preventing automated URL analysis tools from fetching the ISO file."
The malicious payload embedded within the ISO image is a Golang-based downloader dubbed GOGITTER that's responsible for creating a Visual Basic Script (VBScript) file if it does not already exist in the following locations: "C:\Users\Public\Downloads," "C:\Users\Public\Pictures," and "%APPDATA%." The script's purpose is to retrieve VBScript commands from two pre-configured C2 servers every 30 seconds. Additionally, GOGITTER establishes persistence through a scheduled task set up to execute the previously mentioned VBScript file every half an hour.
It also determines whether another file called "adobe_update.zip" is present in the same three folders. It retrieves the archive from a private GitHub repository ("github[. ]com/jaishankai/sockv6") if the ZIP file is not found. On June 7, 2025, the GitHub account was established.
Once the download is successful, the attack chain sends an HTTP GET request to the domain "adobe-acrobat[. ]in" likely to signal the threat actors that the endpoint has been infected. GOGITTER then extracts and executes "edgehost.exe" from the ZIP file.
A lightweight Golang-based backdoor, GITSHELLPAD, leverages threat actor-controlled private GitHub repositories for C2.
In particular, it uses a GET request to poll the C2 server every 15 seconds in order to retrieve the contents of a file called "command.txt." Six commands are supported: cd.., to change the working directory to the parent directory cd, to change the directory to the specified path run, to run a command in the background without recording the output upload, to upload a local file specified by the path to the GitHub repository download, to download a file to the specified path default case, and to run a command using cmd /c and record the output. An HTTP PUT request is used to upload the "result.txt" file containing the command execution results to the GitHub account.
After the command is successfully run, the "command.txt" is removed from the GitHub repository. After gaining access to the victim's computer, Zscaler reported that it saw the threat actor also using cURL commands to download RAR archives. Utilities to collect system data and drop GOSHELL, a custom Golang-based loader that delivers Cobalt Strike Beacon following several decoding rounds, are included in the archives.
After use, the machine's tools are cleaned. "GOSHELL's size was artificially inflated to approximately 1 gigabyte by adding junk bytes to the Portable Executable (PE) overlay, likely to evade detection by antivirus software," the cybersecurity firm stated. "By comparing the victim's hostname against a hard-coded list, GOSHELL only executes on specific hostnames."











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)