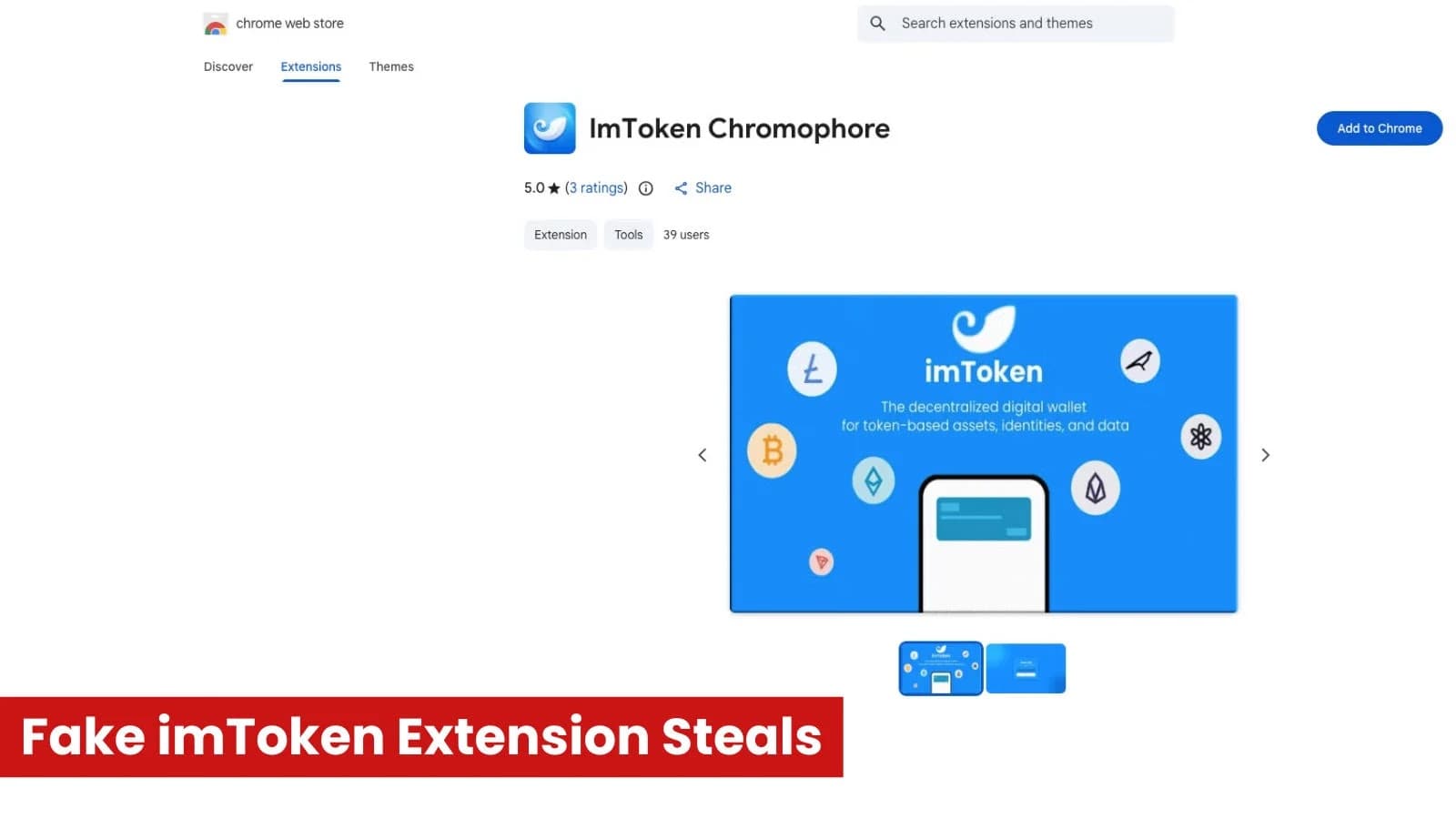
Security experts have discovered a malicious Chrome extension that poses as the well-known cryptocurrency wallet imToken and is intended to steal users' wallet recovery credentials. The "lmToken Chromophore" extension poses as a benign color visualization tool while surreptitiously sending users to phishing websites that steal private keys and seed phrases. The Threat Research Team at Socket identified the malicious extension.
The listing's actual goal is to reroute victims to attacker-controlled websites that imitate the imToken interface, despite its claims to offer a hex color visualization feature. Due to cryptocurrency wallets' reliance on private keys and seed phrases for account access, hackers who manage to get their hands on these secrets can seize victims' money right away. Phishing Redirect Functionality Is Hidden by Extension.
The malicious extension automatically launches a phishing page in a new browser tab after it is installed. The threat actor can remotely update the target destination by retrieving the destination URL from a hardcoded configuration endpoint hosted on jsonkeeper[.]com. The malicious lmToken Chromophore extension imitated the well-known wallet brand identity on imToken's official website in order to seem connected.
(Source: socket) The lookalike domain chroomewedbstorre-detail-extension[. ]com, which imitates the look of an imToken onboarding interface and a Chrome Web Store page, is where the phishing page is hosted. The attackers evade basic detection techniques by using Unicode homoglyphs in the branding to make the website look authentic.
Every time the extension is installed or clicked, it reroutes users to this phishing infrastructure rather than offering the promised color visualization functionality. Using mixed-script homoglyphs to mimic imToken, the extension launches a threat actor-controlled wallet import page on a lookalike phishing domain. (Source: socket) A five-star rating, wallet-themed graphics, and a privacy statement that no data is collected are just a few of the features in the extension listing that are meant to boost trust.
Wallet secrets are captured by phishing websites. After being redirected, victims are led through a phony wallet import procedure that imitates the authentic onboarding process of imToken. Entering a 12- or 24-word seed phrase or supplying a wallet private key are the two recovery options available on the phishing page.
The alternative path provides the threat actor with an additional direct path to wallet access by requesting a plaintext private key. (Source: socket) According to Socket research, the phishing workflow continues with a fictitious password setup screen and a loading message stating that the wallet is being upgraded in order to preserve the appearance of authenticity. The website opens the authentic token in a different browser tab after the victim submits sensitive information, which may lessen suspicion.
Because users frequently trust browser extensions once they are installed, security experts caution that they can act as potent attack vectors. Any browser extension claiming to represent the wallet should be viewed with suspicion because imToken is currently only available as a mobile app and does not provide a Chrome extension.
T1195.002 Supply Chain Compromise T1176.001 Browser Extensions T1059.007 JavaScript Execution T1036 MITRE ATT&CK ID Attack Technique Description T1656 in disguise Mimicking T1566 Phishing