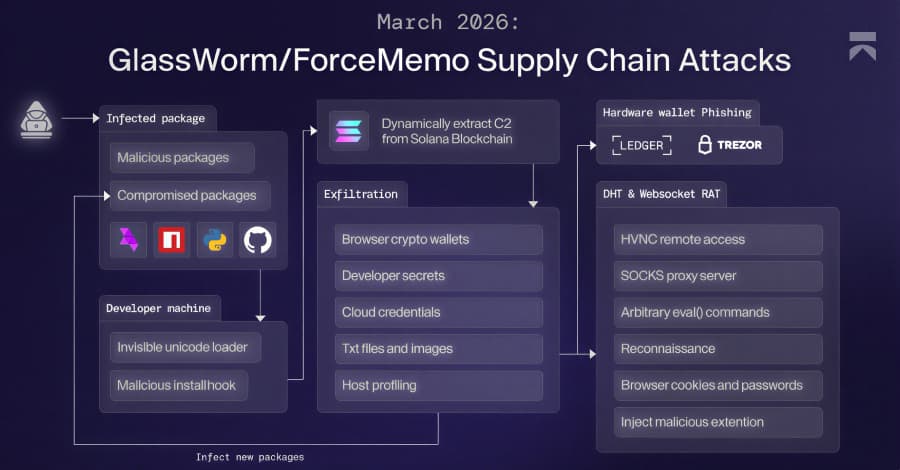
Researchers have noticed a new change in the GlassWorm campaign This article explores glassworm campaign gives. . It gives you a multi-stage framework that can steal all of your data and install a remote access trojan (RAT).
The RAT uses a fake offline version of Google Docs to steal information from Google Chrome. The malware not only stops any real Ledger Live processes that are running on the infected system, but it also shows the phishing window again if the victim closes it. The attack's main goal is to get the wallet recovery phrase and send it in a Solana blockchain memo to the IP address "45.32.150[.]251." The data that was collected is put into a ZIP file and sent to an outside server at "217.69.3[.]152/wall."
It also has the ability to get and run the final payload.
GlassWorm has been pretending to be the WaterCrawl Model Context Protocol (MCP) server in order to spread bad software. The Polish cybersecurity company AFINE has released an open-source Python tool called glassworm-hunter that can be used to look for campaign-related payloads on developer systems. Developers should be careful when installing Open VSX extensions, npm packages, and MCP servers.
It's also a good idea to check the names of publishers and the history of packages, and not just trust download counts. "This is the first time GlassWorm has been confirmed to move into the MCP ecosystem," said Lotan Sery, a Koi security researcher. "And since AI-assisted development is growing so quickly and M CP servers are designed to be trusted, this won't be the last," he said.
Researchers Paweł Woyke and Sławomir Zakrzewski said, "Glassworm-hunter makes no network requests while scanning."