Since May 2025, a new malware known as COLDRIVER—a hacking group with ties to Russia—has undergone multiple developmental iterations. The state-sponsored hacking team has quickly improved and upgraded its malware arsenal, according to Google Threat Intelligence Group (GTIG). The most recent attack waves deviate somewhat from COLDRiver's usual strategy of targeting prominent members of NGOs, policy advisors, and dissidents for credential theft.
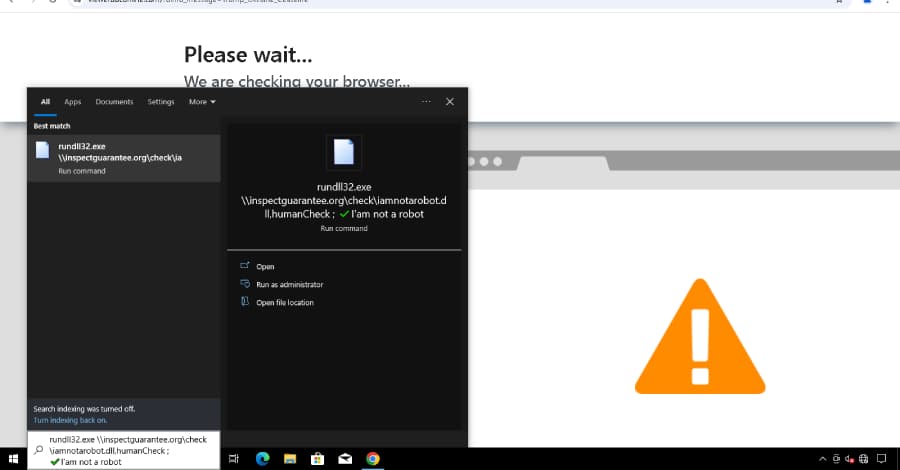
The new infection chain starts with an HTML ClickFix lure called COLDCOPY, which is intended to drop a DLL called NOROBOT, which is then run by rundll32.exe to drop the malware that comes next. Although the duration of the new malware families' development is unknown, GTIG reported that it has not seen any instances of LOSTKEYS since disclosure. On September 22, 2025, two of the suspects were captured.
Due to his "limited role" in the case, the third suspect has been placed under house arrest. "There are no indications yet that pressure has been exerted on the suspect," the Dutch government agency stated. It also stated that the suspect was in communication with a hacker collective connected to the Russian government.
The Dutch authorities stated on Monday that although the case is still being investigated, no arrests have been made as of yet. They stated that no charges or arrests have been made as of yet, and the investigation is still ongoing. The government body stated that although the hacking case is still being investigated, no one has been taken into custody and the suspect is still under house arrest in the Netherlands.
The body also stated that it is unclear if the suspect will be charged in the Netherlands or the United States. Dutch authorities also conducted an interview with him, but he was not detained.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)