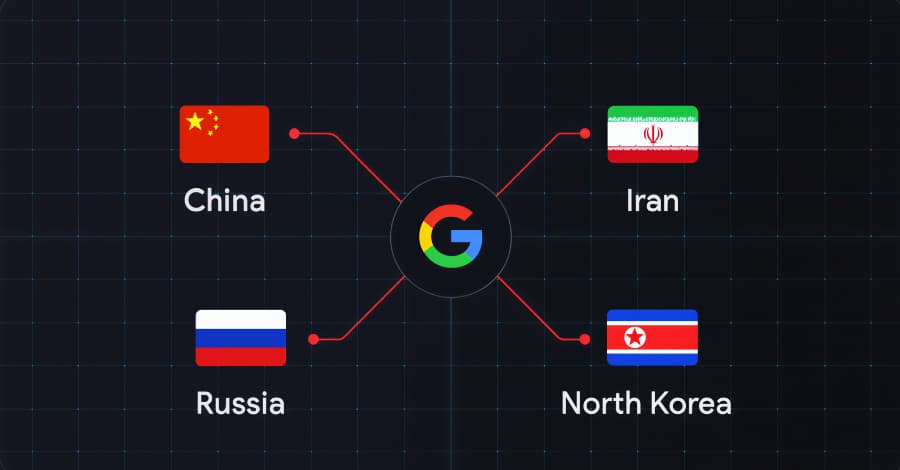
According to research from Google Threat Intelligence Group (GTIG), a number of state-sponsored actors, hacktivist organizations, and criminal organizations from China, Iran, North Korea, and Russia have set their sights on the defense industrial base (DIB) sector This article explores industry attacking defense. . Four main themes, according to the tech giant's threat intelligence division, are at the heart of the adversarial targeting of the industry: attacking defense organizations using technology on the battlefield in the conflict between Russia and Ukraine; directly approaching employees and taking advantage of the hiring process by North Korean and Iranian actors; using edge devices and appliances as first points of entry for groups with ties to China; and supply chain risk resulting from the manufacturing sector breach.
According to GTIG, "as these platforms play an increasing role in modern warfare, many of the chief state-sponsors of cyber espionage and hacktivist actors have shown an interest in autonomous vehicles and drones." "Further, the 'evasion of detection' trend [...] persists, as actors target individual endpoints or conduct intrusions in a way that aims to completely evade endpoint detection and response (EDR) tools." Among the prominent threat actors involved in the activity are: APT44 (also known as Sandworm) has tried to steal data from encrypted messaging apps like Telegram and Signal, most likely after gaining physical access to devices acquired during ground operations in Ukraine.
This includes decrypting and exfiltrating data from Signal's desktop application using a Windows batch script named WAVESIGN. In order to implement a backdoor known as THINWAVE, APT43 (also known as Kimsuky) most likely used infrastructure that imitated German and American defense-related organizations. In addition to using artificial intelligence (AI) tools to conduct reconnaissance on its targets, UNC2970 (also known as Lazarus Group) has carried out the Operation Dream Job campaign to target the aerospace, defense, and energy sectors.
Using malware families like MINIBIKE, TWOSTROKE, DEEPROOT, and CRASHPAD, UNC1549 (also known as Nimbus Manticore) has targeted the Middle Eastern aerospace, aviation, and defense sectors. Under the pretense of genuine job openings, the group is known to plan Dream Job campaigns akin to those of the Lazarus Group, which deceive users into downloading malware or divulging login credentials.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)