In a recent comprehensive report, the Google Threat Intelligence Group (GTIG) highlighted the growing cyber threats to the defense industrial base (DIB), where attacks are now able to penetrate supply chains and servers in addition to battlefields This article explores threats russia nexus. . Hacktivists, criminals, and state-sponsored hackers target manufacturers, contractors, and military personnel that support operations around the world.
Ahead of the Munich Security Conference, this analysis calls for more robust defenses against these multi-vector threats. Russia-nexus actors concentrate on defense technology related to Ukraine, particularly unmanned aerial systems (UAS) and battlefield instruments like the Delta and Kropyva app groups like TEMP and APT44 (Sandworm). Vermin steal data from military devices and contractors using malware like VERMONSTER, lures with a drone theme, and phony Signal invites. DDoS attacks on drone monitoring are claimed by hacktivists such as KillNet, who want to interfere with operations and expose data.
TEMP.Vermin's Lure document (Source: Google) These strategies use Android trojans like GREYBATTLE and WhatsApp phishing to target soldiers on their personal devices that are not under corporate surveillance. GTIG observes that in order to infiltrate Western supporters, actors impersonate defense companies in phishing, such as impersonating Ukrainian drone manufacturers. By compromising next-generation weapons in real time, this persistent campaign advances Russia's war objectives.
Human-Centric Attacks Bypassing perimeter security, adversaries increasingly target workers with personal emails and employment scams. The UNC5125 Google Forms survey claims to be from the Dronarium Drone Training Academy (Source: Google). The 2025 U.S. arrests of facilitators demonstrate how North Korea's IT worker schemes infiltrate defense companies for espionage and financial gain.
Iranian organizations such as UNC1549 and UNC6446 use resume builders to distribute malware by impersonating job portals for aerospace and drone positions. Using event invites or Boy Scout lures for contractor emails, China's APT5 creates hyper-personal phishing. Data from Ukrainian defense staff is made public by pro-Russian doxers like Beregini in an effort to foster mistrust.
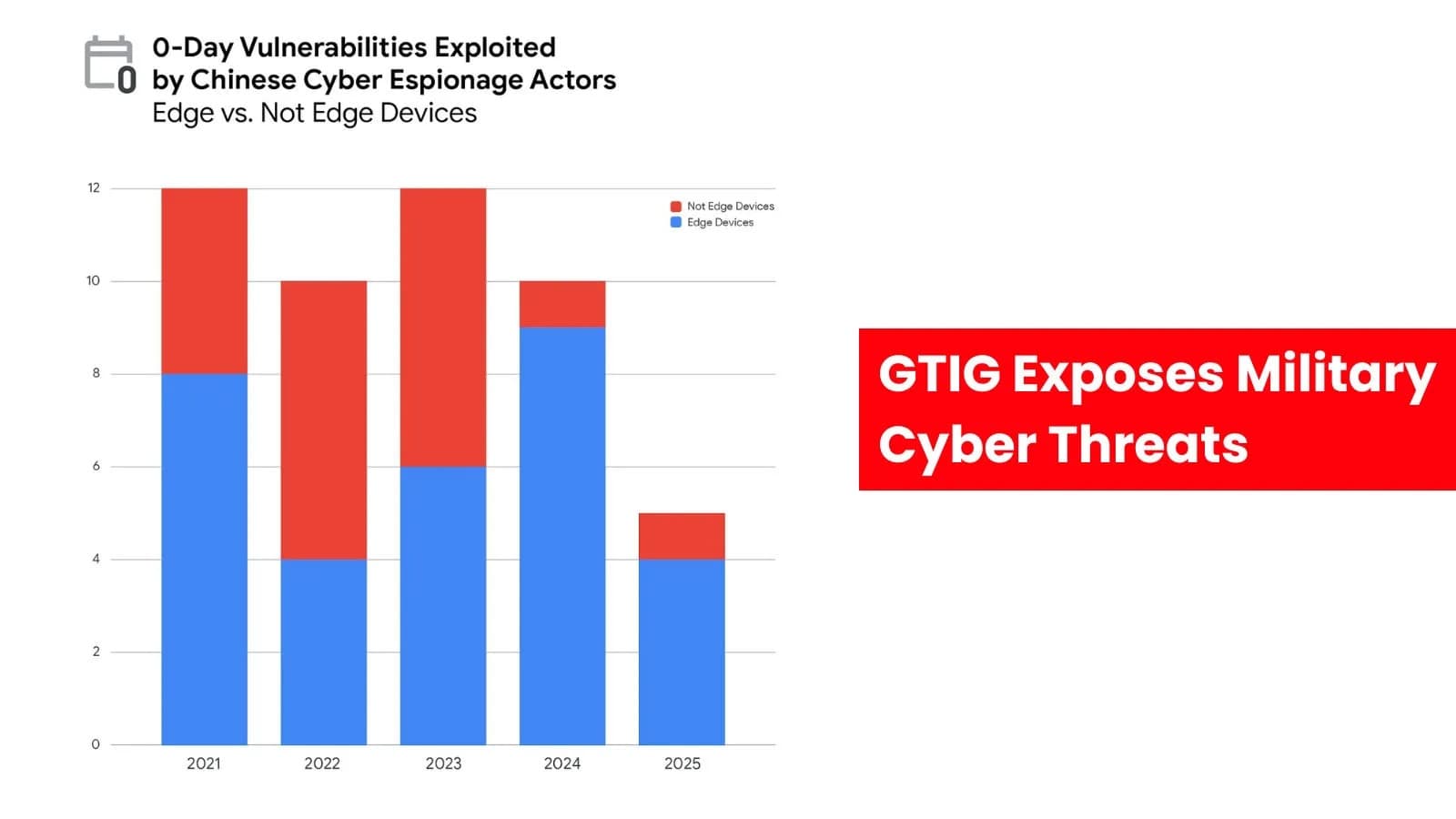
This "human layer" focus avoids endpoint detection, according to GTIG, which calls for improved off-network training. China-Nexus Dominance Since 2020, China-affiliated groups have dominated in terms of volume, using more than two dozen zero-days to exploit edge devices such as routers and VPNs. Stealthy malware, with dwell times of up to 393 days in BRICKSTORM campaigns, is used by UNC3886 and UNC5221 to sustain long-term access to aerospace targets. For intelligence on military systems, they give priority to "force multipliers," like suppliers.
UNC5976 credential harvesting infrastructure was found to be impersonating aerospace and defense companies (Source: Google). APT5 and UNC6508 filter emails for UAS keywords before infiltrating through regulations on U.S. institutions. By targeting IT networks prior to OT disruptions, this edge focus facilitates R&D theft.
Google Cloud claims that manufacturing is the industry most affected by ransomware, with military dual-use parts at risk on data leak websites. Defense readiness hacktivists like Handala Hack dox Israeli companies and leak contracts through supply-chain compromises after a 2025 UK auto breach put a stop to production for weeks. Proactive hunting is emphasized by GTIG: monitor chains, secure edges, and vet hires. These dangers present an increasing threat to international security as defense expenditures increase.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)