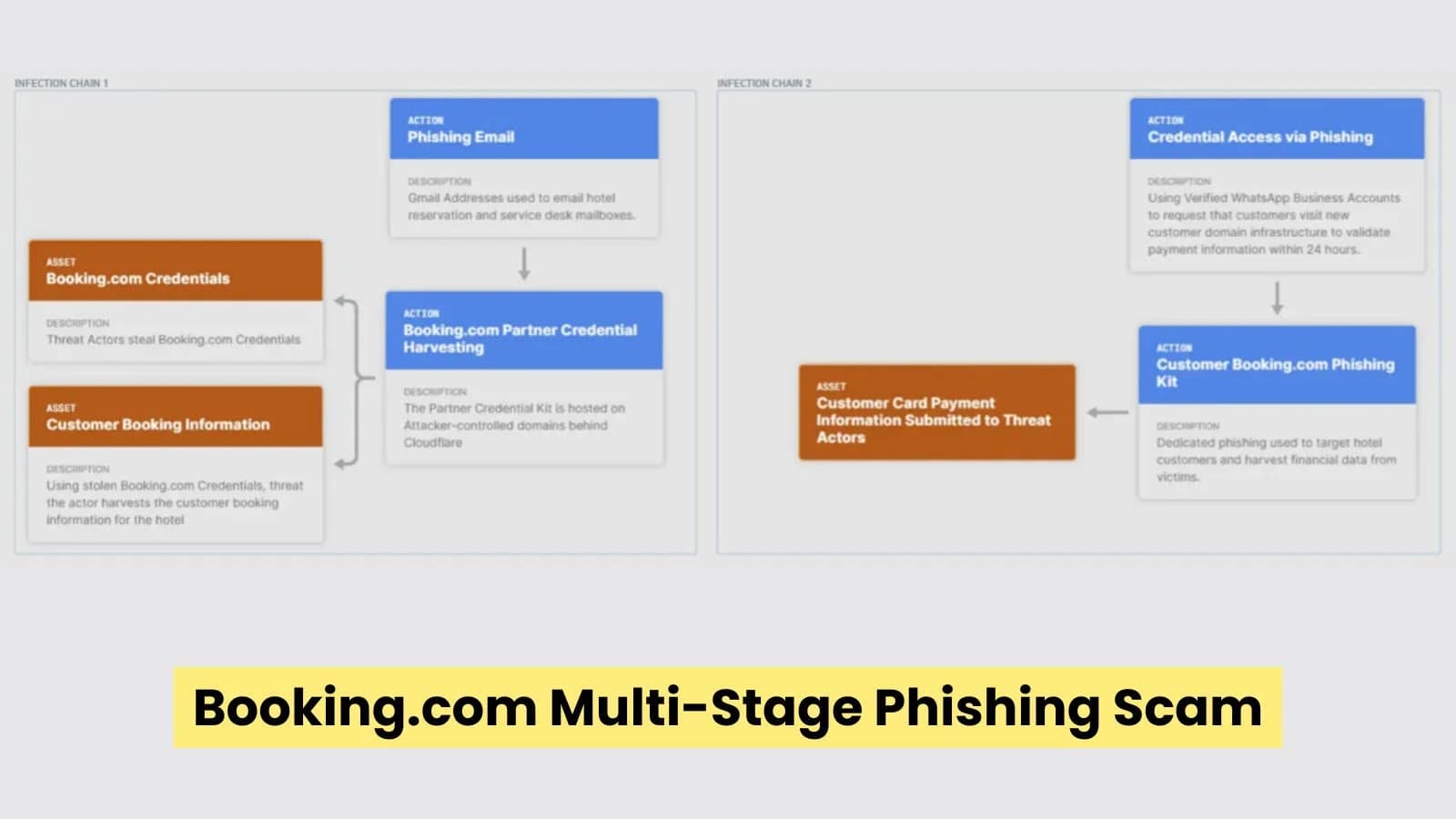
A well-planned, two-step phishing campaign is being used by a recently discovered cybercrime operation to target travelers and hotel employees. According to security experts, the attackers follow an ATT&CK-style flow, in which hotel partners are the target of the first compromise, and customers are defrauded in the second stage by using stolen booking data. The campaign, which has been underway since at least January, exhibits strong defense-evasion strategies, automation, and deceit.
Phase One: Compromise from Partners Phishing emails sent straight to hotel reservation mailboxes start the first infection chain. Numerous Gmail accounts with similar patterns are created by attackers, indicating automated registrations.
The criminals pretend to be Booking.com in these messages, and they call the recipient a "partner." First Question (Source: Bridewell) The emails frequently purport to be regarding an urgent booking issue or a guest complaint. Instead of confirming authenticity, this pressure tactic encourages hotel employees to react fast.
Every email has a link that looks authentic but actually takes the recipient to infrastructure that is under the control of the attacker. Usually, the URLs consist of a query like "complaint?op_token=" followed by a distinct ID. The attackers employ an IDN homograph trick to avoid detection, substituting a Cyrillic character that looks exactly like the Latin "o" in the brand name. Tenant 1 (Bridewell, source) Users and email filters might not notice the difference.
The domains themselves are recently registered and often combine brand words with terms like "portal," "identity," or "management," a tactic known as typosquatting and combo-squatting. The victim is taken to a phony partner login page created by a phishing kit when they click on the link. The pages use an odd HTML structure, putting each letter of the brand name in its own tag, to replicate the look of the actual login portal.
The website steals login information and sends it to the attackers in a covert manner. The phishing infrastructure uses browser fingerprinting to get around security tools. It blocks suspected security researchers or VPN traffic and examines WebGL, screen properties, and other device indicators. A harmless cleaning-service webpage is shown in its place if the visitor doesn't pass the checks.
Stage Two: Data Abuse & Traveler Fraud Once the hotel credentials have been stolen, the criminals access the platform and download booking information, such as names, dates, and reservation IDs. The second infection chain is then started. Travelers receive accurate booking details in WhatsApp messages, sometimes from verified business-style accounts.
Tenant 2 (Bridewell, source) If the customer does not confirm payment, the reservation will be canceled within 24 hours, the message warns. Victims trust the request because the information is authentic. The link takes users to a different phishing page that imitates the payment screen of the booking platform. After the stolen booking information is automatically filled in, the kit reroutes to a CAPTCHA protection page.
The attackers immediately steal money after the victims input their card information.
Technique for Partner Phishing Domains (Samples): extrapp-menus-controls-portal.com Portal ID Management app-htl-manage.com Impersonation mgmnts-ids-center.com Hotel Attractions Bridewell claims that the campaign's impact is substantial because hotels might not become aware of the breach until patrons report fraudulent activity. The scheme seems to be driven by financial gain, taking advantage of the established connection between booking platforms and hotels to deceive both staff and customers. Security professionals recommend that hotels implement multi-factor authentication, train employees to closely examine dubious URLs, and validate complaints via official dashboards.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)