In a mature SOC, escalation should feel more like a knife than a shovel This article explores escalations gives tier. . When escalation rates go above 20%–30%, the problems become clear throughout the alert-handling chain.
Operations with a lot of escalation need bigger teams, longer shifts, and more expensive tools to keep response times reasonable. Analysts work in a fog without timely, relevant threat intelligence. When you're in a fog, everything seems suspicious enough to get worse. For MSSPs, trust in clients fades.
The risk of SLA breaches goes up for SOCs. Costs add up at the business level. New Tier 1 analysts tend to raise issues more. When there isn't strong guidance and context, escalation is the safest choice.
Mistakes happen again and again if Tier 2 doesn't always pass feedback down to Tier 1. People never learn patterns. Change of analysts. Lack of intelligence.
More tools, more logs, and more connections. Detection logic gets louder. There are more false positives.
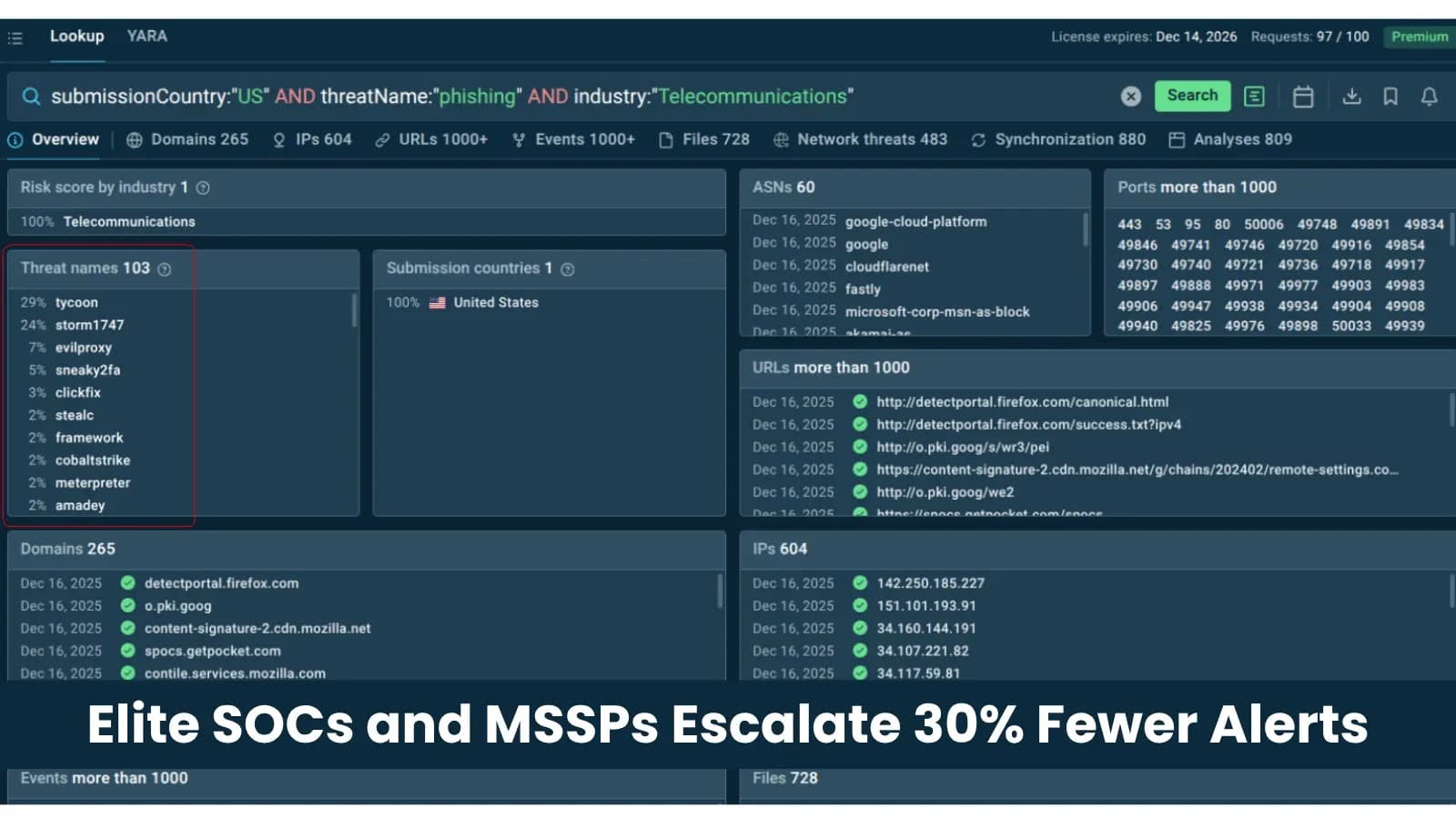
AnyRUN's Threat Intelligence Lookup was made to fix the main data problem that causes unnecessary escalations. It gives Tier 1 analysts instant, on-demand access to constantly updated, context-rich information on any indicator they come across. An analyst doesn't have to look at a flagged IP and escalate it because they can't figure out what it means. Instead, they can see: "This IP was seen as a C2 endpoint in 24 confirmed Emotet detonations in the last 30 days, linked to campaigns that stole personal data from schools in the Asia-Pacific region."
That can be done. That can be closed at Tier 1. It makes Tier 1 very important. It makes responses faster, more accurate, and aligns security operations with business goals.
The benefit isn't just smarter people in the end. It's easier to understand.