Review of SOC analysts' alerts When an alert proves to be harmless, how much time do you spend reviewing it This article explores investigating single alert. ? For many teams, investigating a single alert takes about half an hour.
Not because it's difficult, but rather because you need to gather information from a variety of sources before making a firm decision, including log pivots, enrichment, detonation requests, and reputation checks. At scale, that results in escalation pressure, a growing backlog, increased operational expenses, and a slower reaction to actual threats. What if the majority of benign alerts could be resolved in two minutes on average? Without switching between tools, the sample can drop files, change the registry, or initiate browser activity all within the same session.
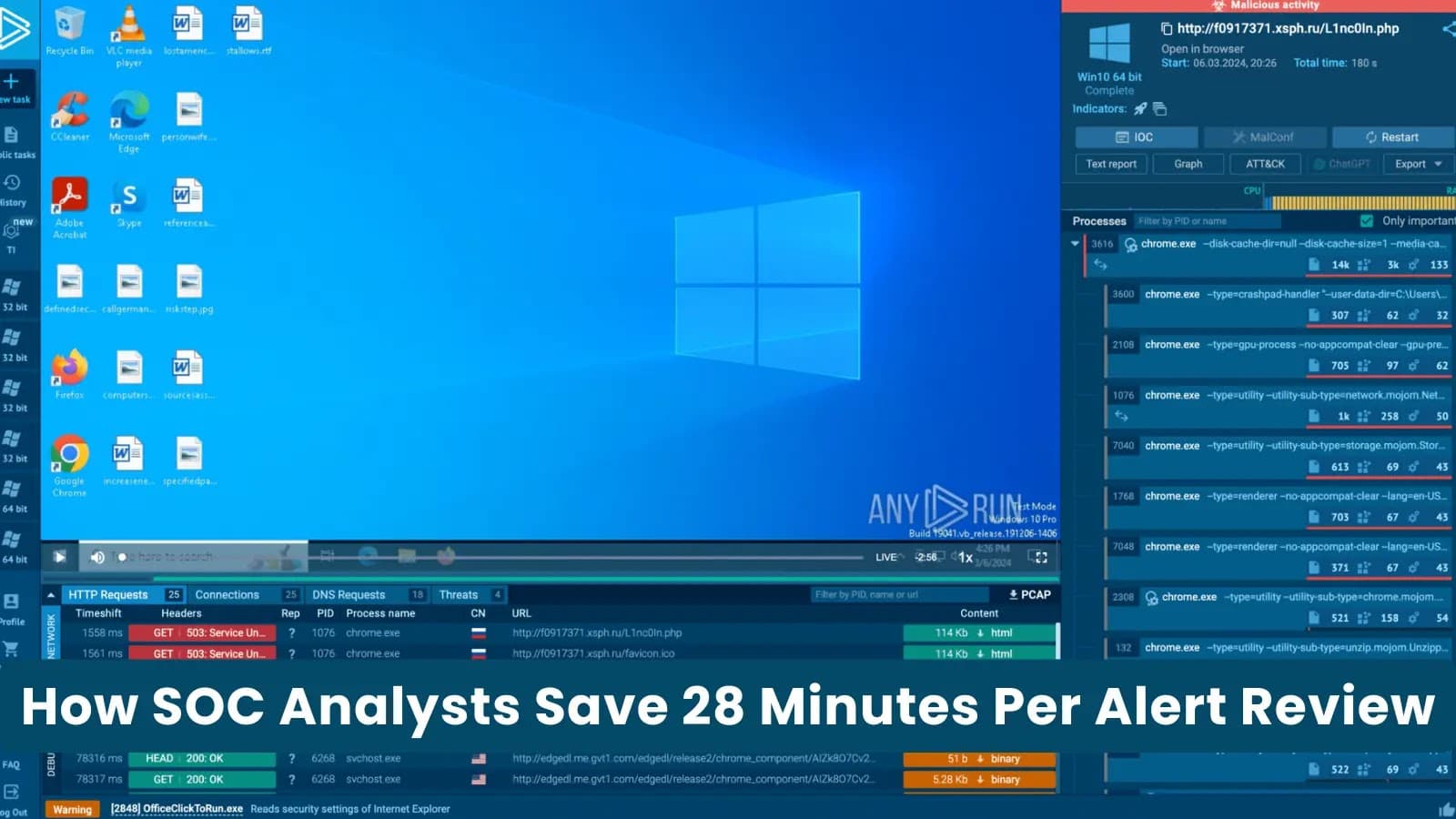
interactive sandbox that displays Tycoon2FA phishing activity, backed up by real-time network evidence and mapped to MITRE. Compromise indicators are automatically gathered and arranged in a specific tab. Everything that was taken out of the session—domains, IPs, hashes, URLs—is accessible without the need to switch tools or manually copy artifacts.
Building your IOC list doesn't require you to switch between views.