Kaspersky says that the Coruna exploit kit is a new version of the same exploit that was used in the Operation Triangulation campaign. Google and iVerify first reported on Coruna earlier this month, saying it was aimed at Apple iPhone models running iOS versions 13.0 to 17.2. The exploit kit has 23 exploits, including CVE-2023-32434 and CVE-2023-38606, as well as five full iOS exploit chains.
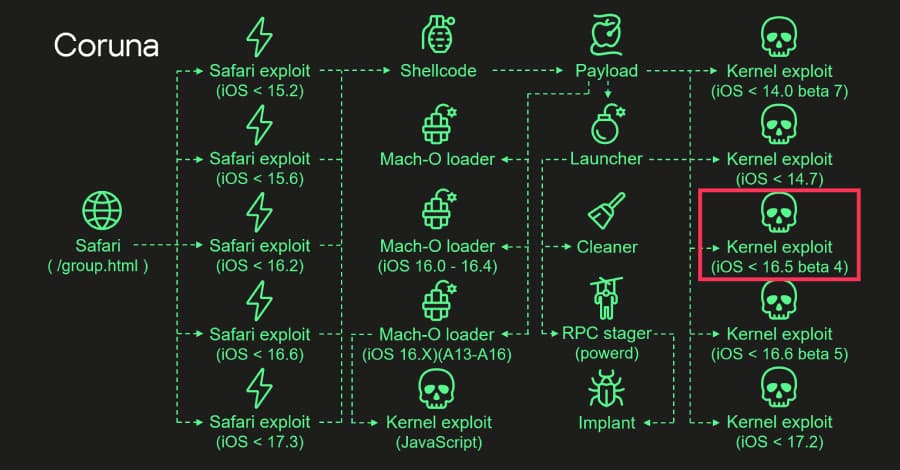
The attack starts when someone visits a hacked website on Safari. This makes a stager fingerprint the browser and send the right exploit based on the version of the browser and operating system. The payload picks the right Mach-O loader based on the firmware version, CPU, and whether or not the iokit-open-service permission is present.
It then uses the kernel exploit to drop and run the final implant, which gets rid of any evidence of the exploit to hide the forensic trail. The news comes as a new version of the iPhone exploit kit DarkSword has been leaked on GitHub. This raises fears that it could give more hackers advanced tools to hack into devices.
A customer of an unnamed surveillance company first used it early last year. Since then, a suspected Russia-aligned nation-state actor has used it in watering hole attacks in Ukraine and in a mass exploitation campaign that used a group of fake Chinese gambling and cryptocurrency websites to spread a data-stealing malware called PlasmaLoader (also known as PLASMAGRID). The code works with Apple's A17, A3, M3 Pro, and M3 Max processors, and it also checks for iOS 17.5 beta 4, which fixed all four vulnerabilities that were used in Operation TriANGulation.