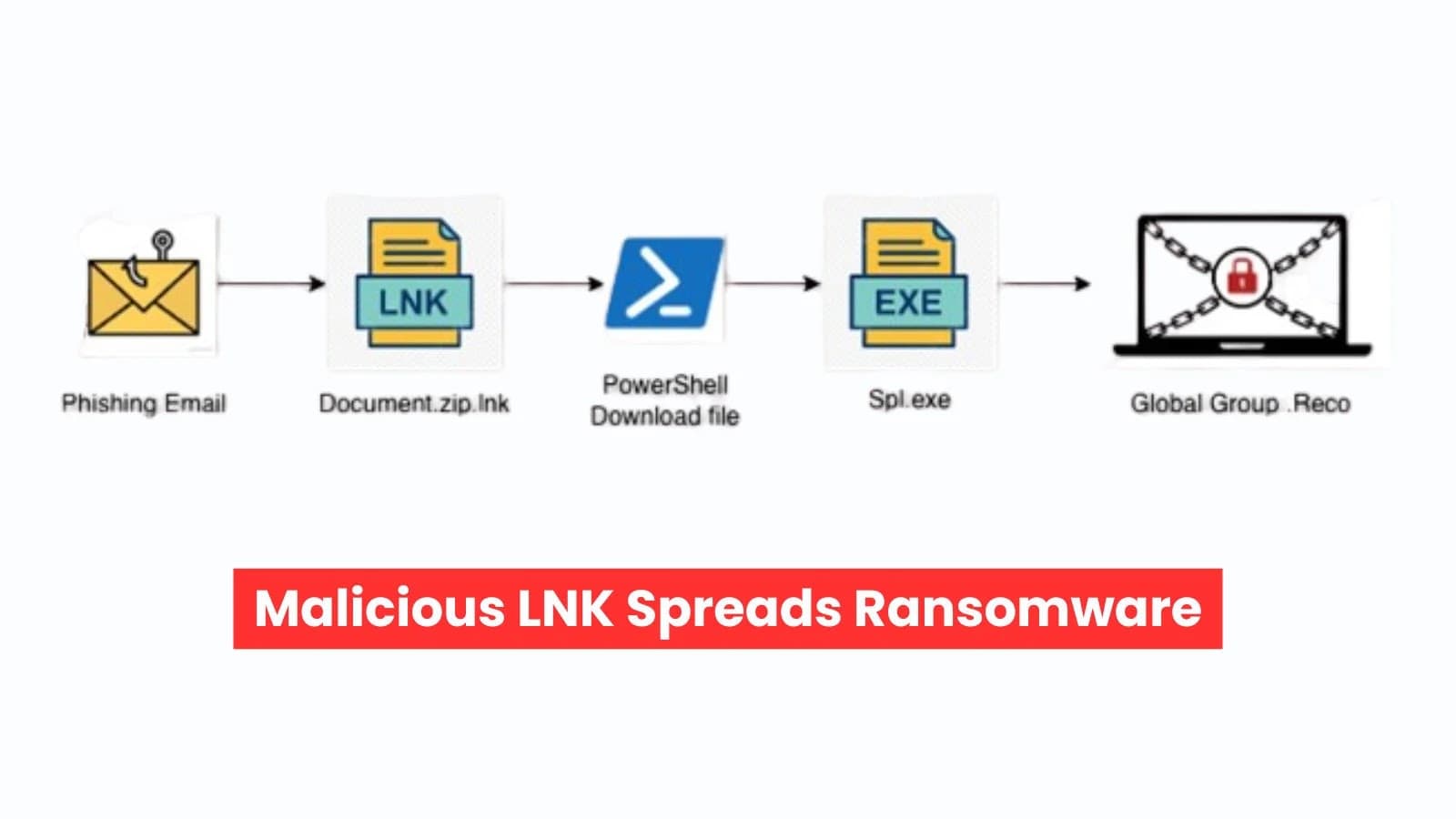
Researchers studying cybersecurity have discovered a massive Phorpiex campaign that is affecting email accounts all over the world This article explores ransomware stealthy new. . Phishing emails with the subject "Your Document" deceive recipients into clicking on a phony attachment.
This is a weaponized Windows shortcut (.lnk) file, not a legitimate Word document. Attackers use a combination of cunning tactics and social engineering to get past security measures and covertly download ransomware. Both home users and businesses were the targets of these attacks, which peaked in late 2025. The objective?
Install GLOBAL GROUP ransomware, a stealthy new danger from the Mamona clan. Hackers create chaos with a single click by using common file types. Why LNK Files Continue to Deceive Defenses Due to their simplicity and stealth, Windows shortcuts continue to be a popular choice among cybercriminals.
Attackers conceal the truth.lnk extension using tricks like "Document.doc.lnk." Because Windows defaults to hiding known extensions, victims only see the innocuous Word document "Document.doc." To make it appear authentic, they pilfer icons from reliable sources, such as shell32.dll.
There are no installers or pop-ups. Rather, the shortcut launches PowerShell or cmd.exe in the background. This "Living off the Land" (LotL) strategy avoids antivirus scans by using Windows' built-in tools. An example of a phishing email (Source: forcepoint) The May 2024 email attachment "Document.doc.lnk" makes reference to recycled tools.
After being clicked, Cmd.exe silently starts up with hidden arguments. To obtain a payload from IP 178.16.54.109, it invokes PowerShell. The file "spl.exe" imitates a Windows driver by downloading as "windrv.exe" in the user's profile.
Without the user's knowledge, PowerShell launches it through Start-Process. This downloader is distributed by the Phorpiex botnet, which has been in operation since 2010. It frequently distributes ransomware, including the Ransomware-as-a-Service (RaaS) group GLOBAL GROUP.
Global Group: Spread and Silent Encryption Global Group is notable for its "mute" mode, which prevents calls to hacker servers. It works offline, generates encryption keys on your computer, and guards against data theft. This outperforms network monitors that keep an eye out for unusual activity. Attachment to an email (Source: forcepoint) The unpacked binary, dropped as "windrv.exe," displays its plans in plain strings.
The first ping trick is "ping 127.0.0.7 -n 3 && del /f /q windrv.exe." This three-second delay lets it encrypt files, then self-deletes to hide tracks. Anti-analysis checks kill virtual machine processes, sandboxes, and tools.
Database apps are also zapped in order to release encrypted files. A copy to Windows\Temp\cleanup provides persistence.exe, an on-demand service, and a "CoolTask" in Task Scheduler (run as SYSTEM, then deleted). It uses LDAP to query Active Directory, establishes remote services, uses ADVAPI32.dll to steal credentials, and deletes event logs in order to propagate.
The command prompt opens PowerShell (from forcepoint) A “README.Reco.txt” note identifies a Tor website, and files are encrypted with ChaCha20-Poly1305, which is stronger than previous versions, according to Forcepoint. It removes shadow copies, leaves notes all over the place, and changes your wallpaper to shout "GLOBAL GROUP." Find it using the mutex "Global\Fxo16jmdgujs437," the wallpaper, or the hex file marker "xcrydtednotstill_amazingg_time!!" This chain demonstrates how well-known techniques like LNK files work with stealthy ransomware.
Pay attention to endpoint alerts for unusual pings, process kills, and cmd/PowerShell downloads rather than just network noise. Block double-file tricks, enable extension views, and educate users about attachments. EDR and other tools detect LotL early.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)