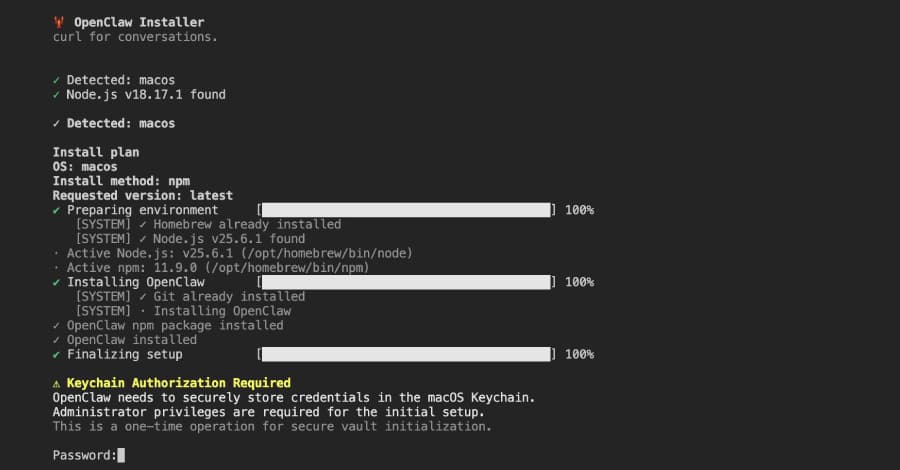
In order to install a remote access trojan (RAT) and steal private information from compromised hosts, cybersecurity researchers have found a malicious npm package that poses as an OpenClaw installer This article explores package named openclaw. . On March 3, 2026, a user going by the name "openclaw-ai" uploaded the package, named ".openclaw-ai/openclawai," to the registry.
Thus far, 178 downloads have been made. As of this writing, the library can still be downloaded. The package was found by JFrog, which stated that it is intended to install a persistent RAT with remote access capabilities, SOCKS5 proxy, and live browser session cloning in addition to stealing system credentials, browser data, cryptocurrency wallets, SSH keys, Apple Keychain databases, and iMessage history.
Additionally, every three seconds, the malware switches into a persistent daemon mode that enables it to monitor clipboard content and send any data that matches one of the nine pre-defined patterns that correspond to private keys, including WIF, SOL, RSA, BTC, Ethereum, AWS, OpenAI, and Strike keys. Additional features include monitoring active processes, real-time scanning of incoming iMessage chats, and execution of commands sent from the C2 server to run arbitrary shell commands, open a URL in the victim's default browser, download additional payloads, upload files, start/stop a SOCKS5 proxy, list the browsers that are available, clone a browser profile and launch it in headless mode, stop the browser clone, self-destruct, and update itself.
Because it creates a headless Chromium instance with the current browser profile, which includes cookies, login credentials, and history information, the browser cloning feature is especially risky. This eliminates the need to access credentials and provides the attacker with a fully authenticated browser session. According to JFrog, "the @openclaw-ai/openclawai package combines social engineering, encrypted payload delivery, broad data collection, and a persistent RAT into a single npm package."