Microsoft's Application Virtualization (App-V) script, SyncAppvPublishingServer.vbs, is used as a living-off-the-land binary (LOLBIN) in a sophisticated Fake CAPTCHA phishing attack to spread Amatera Stealer malware This article explores syncappvpublishingserver vbs powershell. . The campaign places a high priority on stealth, avoiding detection through in-memory execution, third-party infrastructure, and user behavior checks.
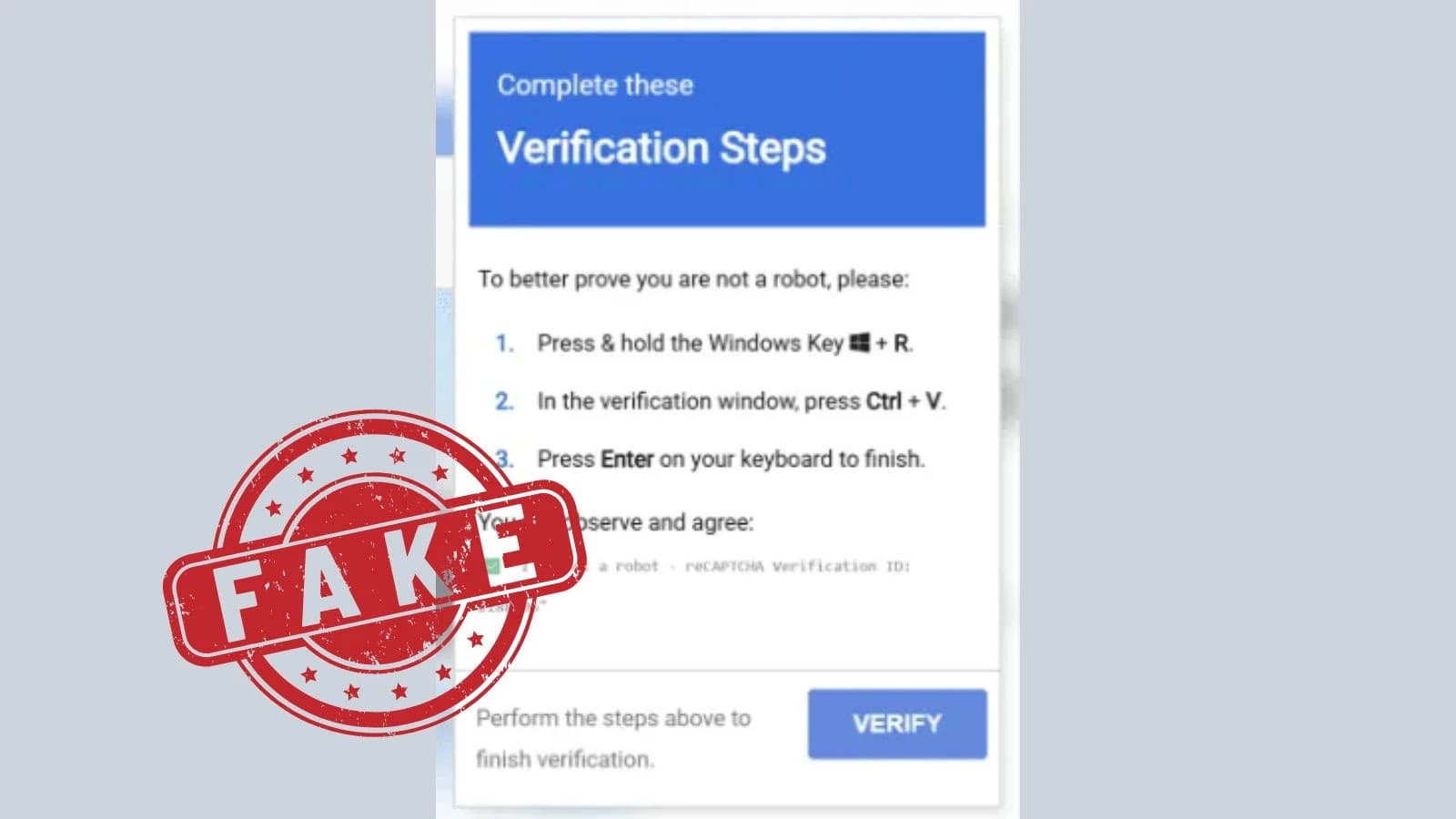
The attack begins with a false CAPTCHA prompt that asks victims to enter a command for "human verification" in the Windows Run dialog. This command starts the signed App-V script to proxy PowerShell execution by launching wscript.exe. This circumvents common detection rules associated with direct PowerShell launches by generating an odd process chain explorer.exe → wscript.exe → SyncAppvPublishingServer.vbs → powershell.exe. App-V components serve as a natural filter; they are included in Windows Enterprise and Education editions but not in Home or Pro.
Sandboxes are frustrated and enterprise environments are targeted when execution fails on unsupported systems. Obfuscation and Execution Gates The first steps involve setting an environment variable called ALLUSERSPROFILE_X and looking for a matching token from the user's manual input in the clipboard. The script uses ManualResetEvent to stall indefinitely if it is absent.WaitOne() shows fake pop-ups.
This gate makes sure that only real user interactions take place. To resolve cmdlets dynamically, PowerShell uses aliases and wildcards, such as "gal i*x" for Invoke-Expression to avoid static strings. Loaders avoid Invoke-WebRequest telemetry by using custom HTTPS routines created with TcpClient and SslStream to fetch obfuscated scripts. Base64 fragments are stored for later use in the first lines of herf54 (Source: blackpoint).
Configuration is retrieved from a public Google Calendar.ics file via a key pivot.
The loader extracts URLs such as sec-t2.fainerkern.ru after parsing a VEVENT with SUMMARY "povvv" and base64-decoding its DESCRIPTION. This "living off others' infrastructure" allows for quick updates without having to redeploy initial phases. Afterwards, an MD5 hash of the environment data is used to create a victim-specific subdomain.
Another loader is downloaded and XOR-decrypted using the key "AMSI_RESULT_NOT_DETECTED." PNG steganography is used in payload delivery from CDNs such as gcdnb.pbrd.co; WinINet APIs retrieve the image; System.Drawing uses LSB to retrieve hidden data from pixel buffers. The payload decompresses to PowerShell and is run in memory after being length-prefixed and XOR-encrypted with the key "s8YUKQ0CqUd6HNwGSRDZ%Qpux1N9MKHh." Shellcode is obtained through final decryption, allocated using NtAllocateVirtualMemory, and executed in a new thread.
This maps Amatera Stealer, an information thief that targets credentials and browsers.
Amatera Stealer Behaviors Amatera spoofs the Host header "cdn.extreme[REDACTED]videos.com" by connecting to 212.34.138.4. For networking, it employs WoW64 syscalls to NtDeviceIoControl, which are layered with SSPI encryption. The final stage PowerShell loader's conceptual logic (Source: Blackpoint) Modular C2 is made possible by a "GetEndpoints" request that retrieves dynamic paths (such as a, b, and c).
Initial CAPTCHA Domain sec-t2.fainerkern.ru Indicator Type Indicator Context Domain cdn.jsdelivr.net Domain of execution gate gcdnb.pbrd.co PNG stego IP 212.34.138.4 Amatera C2 This chain’s reliability stems from signed Microsoft tools, behavior gates, and evasion tactics. It slips past malware-focused defenses, succeeding quietly on enterprise systems. Blackpoint recommends restricting Run dialog access, disabling unused App-V, enabling PowerShell logging, and monitoring anomalous chains like wscript.exe to PowerShell. Alert on Host-SNI mismatches and clipboard accesses in scripts.
Defenders must give delivery paths precedence over endpoints as fake CAPTCHA lures become more common.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)