Microsoft is drawing attention to Storm-2372, an emerging threat cluster. Since August 2024, it has been linked to a fresh wave of cyberattacks targeting various industries. In Europe, North America, Africa, and the Middle East, the attacks have targeted government, non-governmental organizations (NGOs), information technology (IT) services and technology, defense, telecommunications, health, higher education, and the energy/oil and gas sectors.
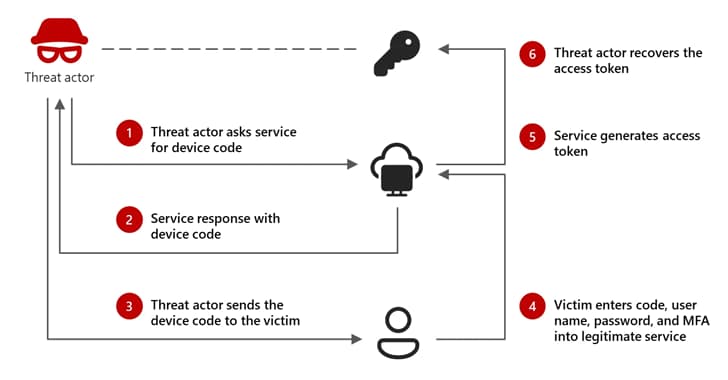
The threat actor has been seen using messaging apps like WhatsApp, Signal, and Microsoft Teams to target users by pretending to be a well-known person who is relevant to the target in an effort to gain trust. It has been determined with medium confidence that the threat actor is aligned with Russian interests, victimology, and tradecraft. The objective is to use the authentication codes acquired through the method to gain access to target accounts, then misuse that access to obtain private information.
It has been determined that some of the emails were sent from accounts posing as representatives of the European Union Parliament, the Ukrainian Ministry of Defense, the US Department of State, and other well-known research organizations. APT29, also known as BlueBravo, Cloaked Ursa, CozyLarch, and Midnight Blizzard (formerly Nobelium), is thought to be one of the clusters responsible for the activity. The other two groups have been given the names UTA0304 and UTA
0307.
According to an analysis by Charlie Gardner, Steven Adair, and Tom Lancaster of Volexity, "it appears that these Russian threat actors have made a concerted effort to launch several campaigns against organizations with a goal of simultaneously abusing this method before the targets catch on and implement countermeasures." The researchers speculated that this might be the result of a single threat actor operating several distinct campaigns.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)