Microsoft has warned that new campaigns are taking advantage of the upcoming tax season in the U.S This article explores malware email campaigns. . to steal personal information and spread malware.
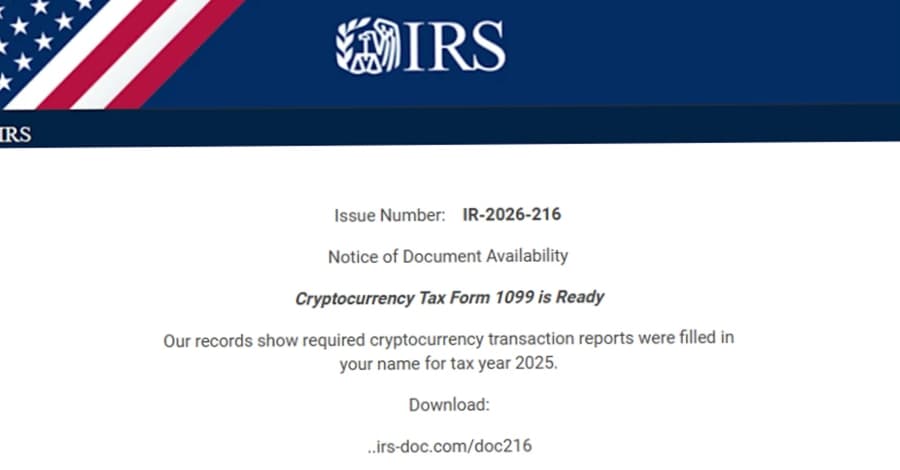
The email campaigns use the fact that emails are time-sensitive and urgent to send phishing messages that look like refund notices, payroll forms, filing reminders, and requests from tax professionals. These messages trick people into opening dangerous attachments, scanning QR codes, or clicking on links that look suspicious. "Many campaigns go after people to steal personal and financial information, but some go after accountants and other professionals who work with sensitive documents, have access to financial data, and are used to getting tax-related emails at this time of year," the Microsoft Threat Intelligence and Microsoft Defender Security Research teams said in a report that came out last week.
Some of these efforts send users to sketchy pages made by Phishing-as-a-Service (PhaaS) platforms, while others install real remote monitoring and management tools (RMMs) like ConnectWise ScreenConnect, Datto, and SimpleHelp. This gives the attackers permanent access to the devices they have compromised. The development happened at the same time as the discovery of several campaigns that drop remote access malware or steal data.
For example, fake Google Meet and Zoom pages are used to trick people into making fake video calls that end up delivering remote-access software like Teramind, a real employee monitoring platform, through a fake software update.
Using a fake website that uses the Avast brand to trick French-speaking people into giving their full credit card information as part of a refund scam. Using a typosquatted website that looks like the real Telegram download portal ("telegrgam[. ]com") to spread trojanized installers that drop a real Telegram installer and run a DLL that starts an in-memory payload.
The malware then connects to its command-and-control network to get instructions, download new parts, and keep access open. Using Microsoft Azure Monitor alert notifications to send callback phishing emails that use fake invoices and payment requests.