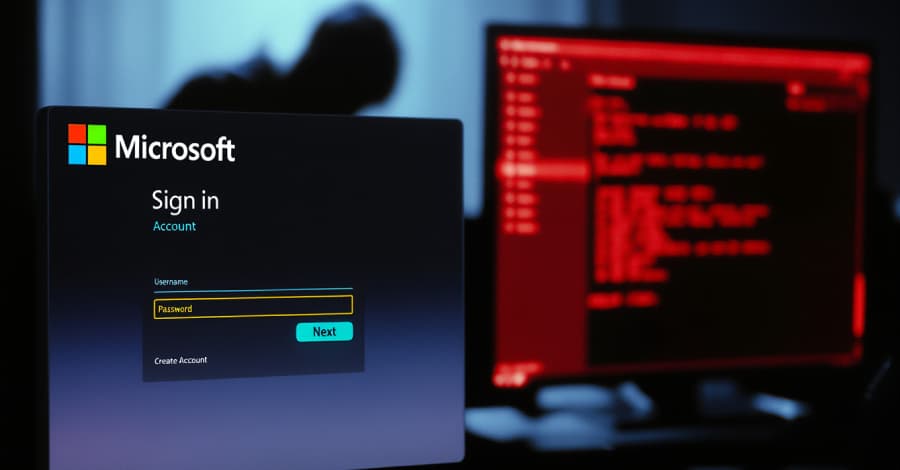
Researchers studying cybersecurity have found what they claim to be the first malicious Microsoft Outlook add-in ever found in the wild. An unidentified attacker used the domain linked to a now-abandoned legitimate add-in to host a phony Microsoft login page, stealing over 4,000 credentials in the process, according to Koi Security's description of this unusual supply chain attack. The cybersecurity firm has given the activity the codename AgreeToSteal.
Koi's co-founder and CTO, Idan Dardikman, told ZeroOwl that the incident shows that supply chain attack vectors have expanded. According to Dardikman, "this is the same class of attack we've seen in browser extensions, npm packages, and IDE plugins: a trusted distribution channel where the content can change after approval."
The add-in is still available in the store, but the same URL is currently hosting a phishing kit. Koi suggests several actions Microsoft can take to address the security risks posed by the threat: - Conduct a re-evaluation when the URL of an add-in begins to return different content than it did during review. Check the domain's ownership to make sure the add-in developer is in charge of it, and mark add-ins where the domain infrastructure has been transferred.
Put in place a system for flagging or delisting add-ins that haven't been updated in a predetermined amount of time. One way to measure impact is to look at display installation counts. Microsoft has been contacted by ZeroOwl for comment; if we hear back, we'll update the story.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)