In order to enable extensive data theft from compromised endpoints, threat actors with connections to China have been seen utilizing an updated version of a backdoor known as COOLCLIENT in cyberespionage attacks in 2025 This article explores backdoor known coolclient. . Mustang Panda (also known as Earth Preta, Fireant, HoneyMyte, Polaris, and Twill Typhoon) has been blamed for the activity, with the intrusions mainly targeting government organizations spread throughout campaigns in Myanmar, Mongolia, Malaysia, and Russia.
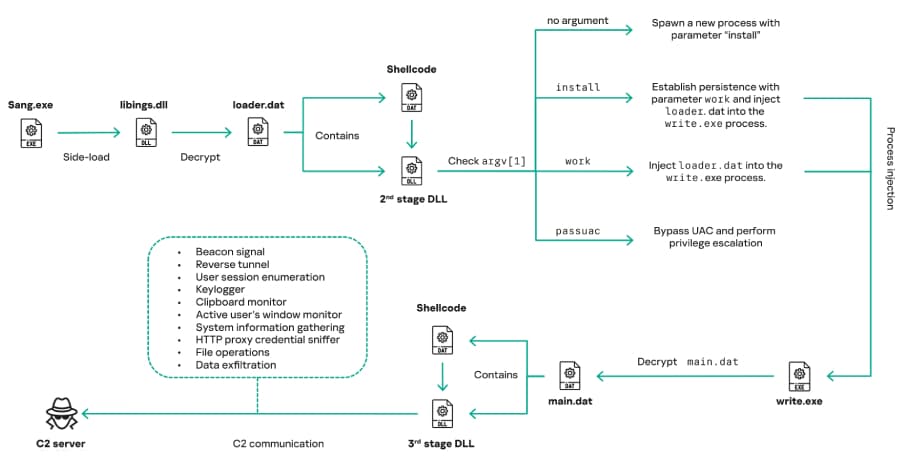
The updated malware is used as a secondary backdoor alongside PlugX and LuminousMoth infections, according to Kaspersky, which released information about it. According to the Russian cybersecurity firm, "COOLCLIENT was usually delivered alongside encrypted loader files containing encrypted configuration data, shellcode, and in-memory next-stage DLL modules."
"The main method of execution for these modules was DLL side-loading, which needed a valid signed executable to load a malicious DLL." Bitdefender ("qutppy.exe"), VLC Media Player ("vlc.exe" renamed as "googleupdate.exe"), Ulead PhotoImpact ("olreg.exe"), and Sangfor ("sang.exe") are among the software products from which Mustang Panda allegedly used signed binaries between 2021 and 2025. Additionally, Mustang Panda has been found to use PowerShell and batch scripts to steal browser login credentials, steal documents, and collect system data.
"HoneyMyte's campaigns seem to go far beyond traditional espionage goals like document theft and persistence, with capabilities like keylogging, clipboard monitoring, proxy credential theft, document exfiltration, browser credential harvesting, and large-scale file theft," the company stated.
"These tools indicate a shift toward the active surveillance of user activity that includes harvesting proxy credentials, recording keystrokes, and gathering clipboard data."











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)