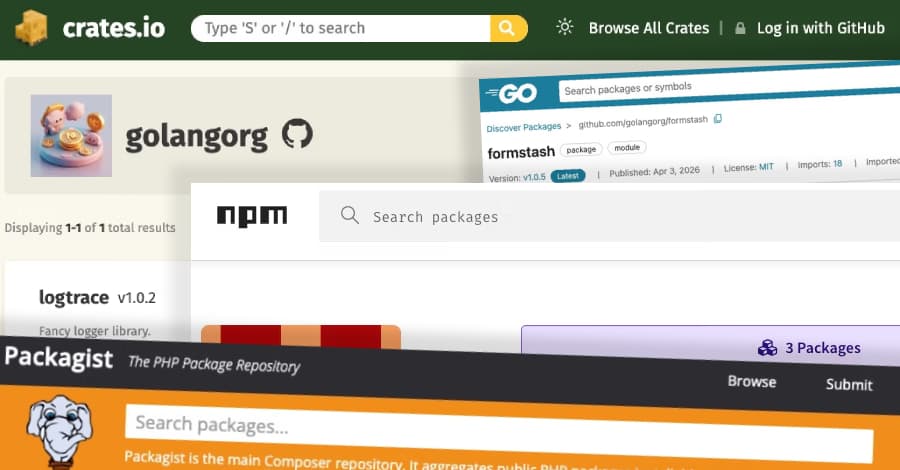
The North Korea-linked persistent campaign called Contagious Interview has grown by sending out harmful packages that target the Go, Rust, and PHP ecosystems. The newest set of libraries is different because the bad code isn't turned on when you install them. Instead, it's hidden in functions that look like they do what the package says they do.
This campaign is interesting not only because it reaches across ecosystems, but also because at least part of the operation has a lot of post-compromise functionality built in. There was a new breach in the software supply chain, which is part of a bigger plan by North Korean hackers. The attack used a harmful implant called WAVESHAPER.V2 to poison the Axios npm package, which is used by a lot of people.
This happened after a targeted social engineering campaign took over the npm account of the package's maintainer. Socket has found more than 1,700 malicious packages involved in the activity as of January 1, 2025. The fact that Contagiously Interview is spreading to five open-source ecosystems is another sign that this campaign is a well-funded and ongoing supply chain threat that is using these platforms as starting points for spying and making money.
"Sherrod DeGrippo, General Manager of Threat Intelligence at Microsoft," said. "We are consistently observing a continuous evolution in how DPRK-linked, financially motivated actors operate, shifting their tooling, infrastructure, and targeting methods while maintaining clear continuity in behavior and intent."
From February 6 to April 7, 2026, the Security Alliance (SEAL) stopped 164 domains that were pretending to be Microsoft Teams and Zoom services. These fake meeting links are used to spread ClickFix-like lures, which then run malware that targets Windows, macOS, and Linux systems.