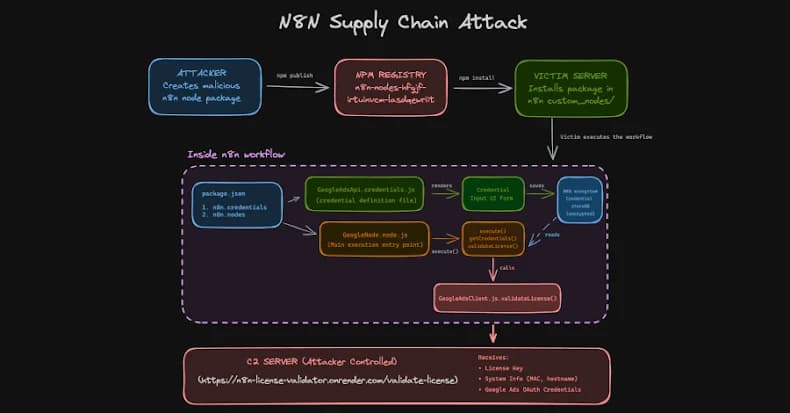
In order to obtain developers' OAuth credentials, threat actors have been seen uploading eight packages to the npm registry under the guise of integrations intended for the n8n workflow automation platform This article explores credentials n8n nodes. . One such package, called "n8n-nodes-hfgjf-irtuinvcm-lasdqewriit," imitates a Google Ads integration and asks users to connect their advertising account in a way that looks authentic before siphoning it to servers that are controlled by the attackers.
"The attack represents a new escalation in supply chain threats," according to a report released last week by Endor Labs.
"This campaign took advantage of workflow automation platforms that function as centralized credential vaults—holding OAuth tokens, API keys, and sensitive credentials for dozens of integrated services like Google Ads, Stripe, and Salesforce in a single location—unlike traditional npm malware, which frequently targets developer credentials." N8n-nodes-hfgjf-irtuinvcm-lasdqewriit (4,241 downloads, author: kakashi-hatake) n8n-nodes-ggdv-hdfvcnnje-uyrokvbkl (1,657 downloads, author: kakashi-hatake) n8n-nodes-vbmkajdsa-uehfitvv-ueqjhhhksdlkkmz (1,493 downloads, author: hezi109) n8n-nodes-performance-metrics (752 downloads, author: zabuza-momochi) n8n-nodes-dane Additionally, the users "zabuza-momochi," "dan_even_segler," and "diendh" have been linked to additional libraries that can still be downloaded as of this writing. - @diendh/n8n-nodes-tiktok-v2 (218 downloads) n8n-nodes-zl-vietts (6,357 downloads) n8n-nodes-gg-udhasudsh-hgjkhg-official (2,863 downloads) n8n-nodes-danev-test-project (1,259 downloads) It's unclear if they have comparable malicious capabilities.
Nevertheless, no security flaws have been found in an evaluation of the first three packages on ReversingLabs Spectra Assure. Regarding "n8n-nodes-zl-vietts," the analysis has identified a component with malware history in the library. It's interesting to note that just three hours ago, an updated version of the package "n8n-nodes-gg-udhasudsh-hgjkhg-official" was published to npm, indicating that the campaign may still be in progress.
Once installed as a community node, the malicious package displays configuration screens and saves the Google Ads account OAuth tokens in encrypted format to the n8n credential store, just like any other n8n integration. When the workflow is carried out, code is run to exfiltrate the tokens to a distant server after decrypting them using n8n's master key.
This is the first time a supply chain threat has specifically targeted the n8n ecosystem, with malicious actors using community integration trust as a weapon to further their objectives. The results draw attention to the security risks associated with incorporating untrusted workflows, which may increase the attack surface. It is advised that developers use official n8n integrations, examine package metadata for any irregularities, and audit packages before installing them.
Additionally, N8n has issued a warning regarding the security risk associated with using community nodes from npm, which it claims can carry out malicious actions on the machine that the service is running on. It is recommended to set N8N_COMMUNITY_PACKAGES_ENABLED to false in order to disable community nodes on self-hosted n8n instances.
"Community nodes have the same degree of access as n8n. According to researchers Kiran Raj and Henrik Plate, "they can read environment variables, access the file system, make outbound network requests, and—most importantly—receive decrypted API keys and OAuth tokens during workflow execution." "Node code and the n8n runtime are not isolated or sandboxed."
"For attackers, the npm supply chain offers a quiet and highly effective entry point into n8n environments. As a result, a single malicious npm package is sufficient to gain deep visibility into workflows, steal credentials, and communicate externally without raising immediate suspicion."











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)