Recently, ANY.RUN, a top provider of interactive malware analysis and threat intelligence solutions, has seen a rise in phishing activity that takes advantage of Microsoft's OAuth Device Code flow This article explores attackers quickly microsoft. . In just one week, they found more than 180 phishing URLs.
Attackers can get OAuth tokens and access corporate M365 environments without stealing credentials by tricking victims into completing a legitimate Microsoft authentication step. This makes detection harder and increases security risks for businesses.
Why This Attack Is a Big Risk for Businesses SOC teams have a harder time finding this attack for a number of reasons: Victims log in to real Microsoft domains You can enter your credentials and MFA on real login pages. The activity takes place entirely over encrypted Traffic over HTTPS Tokens, not stolen passwords, give people access. This means that attackers can quickly get into Microsoft 365 and access corporate email, internal documents, and collaboration platforms.
In some cases, refresh tokens can let attackers keep access, turning one phishing email into data exposure, business email compromise, or even a full account takeover.
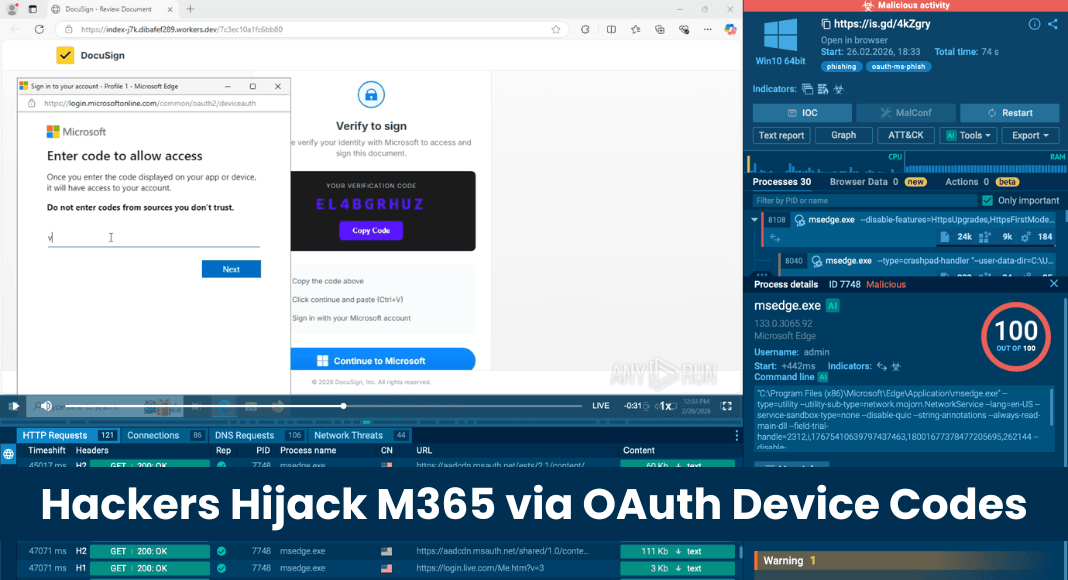
How the OAuth Device Code Phishing Attack Works This is a real-life example of this phishing attack that was found during an analysis in the ANY.RUN sandbox: See the attack that was revealed in the ANY.RUN sandbox OAuth Device Code phishing attack. In this case, the phishing workflow pretends to be a document-sharing service and leads the victim through a series of steps that seem real. This helps teams find related activity faster and stop phishing campaigns like OAuth Device Code before they spread across corporate M365 accounts.
It gets its power from new threat intelligence from 600,000 security professionals in more than 15,000 organizations around the world.
ANY.RUN's connectors and integrations bring new threat intelligence directly into your current stack. Make SOC Operations Better with Interactive Sandbox Analysis. Organizations that use ANY.RUN's interactive sandbox in their security operations say that their investigations go faster and their SOCs work better.
Teams that use the platform have done: Faster checking of suspicious files and links can cut Tier 1 work by up to 20%. 30% fewer escalations from Tier 1 to Tier 2, which lets senior specialists focus on more complicated threats 21-minute reduction in MTTR per case, which makes it possible to contain active incidents faster 94% of users said that daily investigation workflows went faster. Replace hardware sandboxes with a scalable cloud environment to lower infrastructure costs.
Less risk of a breach because threats are found earlier and response decisions are better informed Interactive sandbox analysis helps organizations move from alerts that aren't clear to response decisions that are confident faster by giving security teams clear behavioral evidence of threats. This lowers the operational pressure on the entire SOC.
Use ANY.RUN to make your SOC operations stronger. This will lower the pressure to escalate, speed up triage, and make it easier to find new phishing threats.