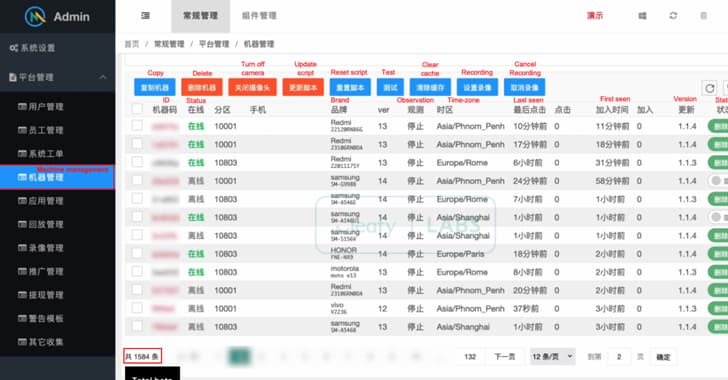
A new strain of Android banking malware has infected more than 1,500 Android devices. Threat actors can carry out fraudulent banking transactions thanks to ToxicPanda. The malware is thought to have been created by a threat actor who speaks Chinese.
It is fundamentally similar to another Android malware known as TgToxic, which has the ability to steal money and login credentials from cryptocurrency wallets. Cleafy researchers also believe that the banking trojan is still in its early stages. DVa, short for Detector of Victim-specific Accessibility, is a malware analysis service that identifies malware that takes advantage of Android devices' accessibility features.
Using dynamic execution traces, including logging data, dead code, and debugging files, the DVa service can detect and link abuse routines to victims. Although it's unclear how these links spread and whether malvertising or smishing techniques are used, it's thought the malware poses as well-known apps. A trojan called ToxicPanda uses Android's accessibility features to overlay fake login pages over trustworthy banking applications.
The malware targets a number of well-known organizations, including Airbnb, Bank of Queensland, Citibank, Coinbase, PayPal, Tesco, and Transferwise. Under a malware-as-a-service (MaaS) model, the malware is sold on Telegram to other criminal actors. A weekly subscription costs $80, while a six-month subscription costs $640.
Google Play Protect, which is enabled by default on Android devices with Google Play Services, automatically protects Android users against known versions of this malware. ToxicPanda's discovery comes after a Netcraft report that described HookBot (also known as Hook), another Android banking malware that takes advantage of Android's accessibility features. There are currently no apps on Google Play that contain this malware, according to our detection.
Google Play Protect has the ability to alert users or block apps that are known to behave maliciously.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)