According to Kaspersky, the new activity was discovered in October
2025.
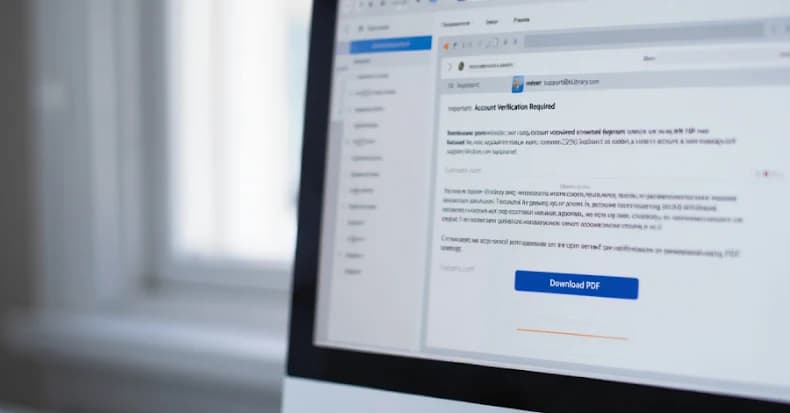
The threat actor's origins are currently unknown. Forum for OperationsTrolls are a group of sophisticated phishing attacks that take advantage of a zero-day vulnerability in Google Chrome. Emails purporting to be from eLibrary, a Russian scientific electronic library, with the address "support@e-library[.]wiki" are another way that the most recent attack wave starts.
According to Kaspersky, the domain was registered in March 2025, six months prior to the campaign's launch, indicating that planning for the attack had been going on for some time. The revelation coincides with Positive Technologies' disclosure of two threat clusters: QuietCrabs, a suspected Chinese hacking group also monitored as UTA0178 and UNC5221, and Thor, which seems to be engaged in ransomware assaults since May
2025.
According to researchers Alexander Badayev, Klimentiy Galkin, and Vladislav Lunin, "Thor is a threat group first observed in attacks against Russian companies in
2025." In a blog post on Monday, Positive Technologies stated, "The attackers use LockBit and Babuk ransomware as final payloads, as well as Tactical RMM and MeshAgent to maintain persistence." Additionally, the company described the attacks conducted by QuietCrab's sister group, QuietCrabb, which has been attacking individuals and organizations in Belarus and Russia since at least 2022.
According to the company, it is likely that this APT group will continue to target organizations and people of interest in these two nations. Additionally, the group described how it makes use of Babuk, LockBit, and other tools. to transfer its payloads to the computer of the victim.
Tuoni, a command-and-control (C2) and red teaming framework, is the final payload that gives the threat actors remote access to a victim's Windows device.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)