A new look at a local privilege escalation flaw in the Windows Error Reporting (WER) service makes it easy for hackers to get full SYSTEM access This article explores patch wersvc dll. . Microsoft thought the flaw, which was tracked as CVE-2026-20817, was so dangerous that it completely removed the feature that was vulnerable instead of trying to fix it with a regular code patch.
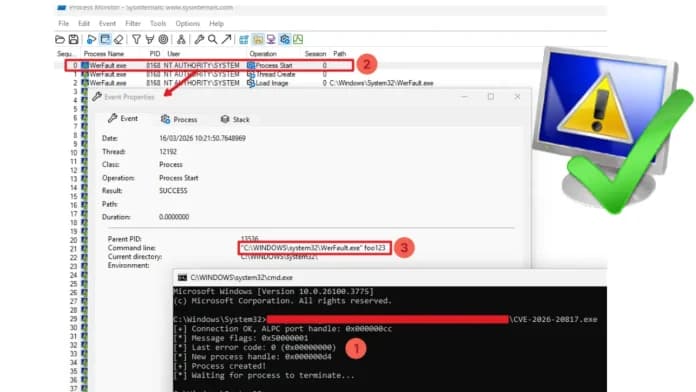
The WerSvc.dll file in the main executable library of the Windows Error Reporting service has a security hole. Denis Faiustov and Ruslan Sayfiev, two vulnerability researchers at GMO Cybersecurity, say that the service doesn't handle insufficient permissions correctly when processing certain client requests. The main part of this vulnerability is changing Advanced Local Procedure Call (ALPC) messages sent to the \WindowsErrorReportingServicePort endpoint.
Finally, the CreateElevatedProcessAsUser function is called, which accidentally starts the real WerFault.exe program with SYSTEM rights and the attacker's tightly controlled settings. There are a lot of fake and possibly harmful proof-of-concept repositories on sites like GitHub. These fake project files often have hidden malware payloads, which is a very important reminder to carefully isolate and analyze all downloaded security tools before running them.
Learn more about security awareness training Tools for network security Deals on security software Security analysts who did binary diffing between versions 10.0.26100.7309 and 10.1.2.7623 of the Wer svc.dl file found that Microsoft took an unusually aggressive approach to fixing the problem. Security programs like Microsoft Defender look for suspicious behavior and send out alerts right away. When looking into this particular local privilege escalate threat, cybersecurity experts need to be very careful.
To get private help, call the Samaritans at 08457 90 90 90, go to a nearby Samaritans branch, or click here for more information.