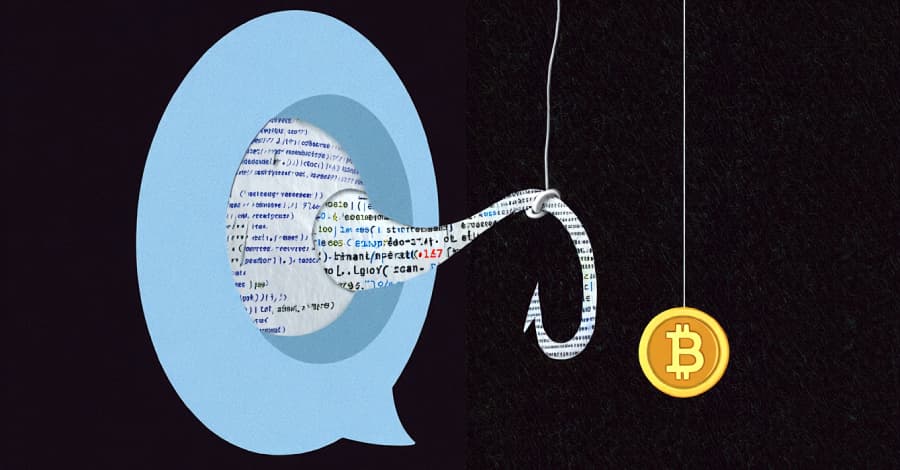
UNC1069, a threat actor with ties to North Korea, has been seen targeting the cryptocurrency industry in an attempt to obtain private information from Windows and macOS systems in order to facilitate financial theft This article explores unc1069 threat. . According to Google Mandiant researchers Ross Inman and Adrian Hernandez, "the intrusion relied on a social engineering scheme involving a compromised Telegram account, a fake Zoom meeting, a ClickFix infection vector, and reported usage of AI-generated video to deceive the victim."
UNC1069, which has been active since at least April 2018, has a history of using phony meeting invites and impersonating investors from respectable companies on Telegram to carry out social engineering campaigns for financial gain. The larger cybersecurity community also keeps tabs on it under the names MASAN and CryptoCore.
The threat actor uses generative artificial intelligence (AI) tools like Gemini to create lure material and other cryptocurrency-related messaging in order to support its social engineering campaigns, according to a report released by Google Threat Intelligence Group (GTIG) last November. A follow-on Golang backdoor component called HIDDENCALL gives hands-on keyboard access to the compromised system and deploys a Swift-based data miner called DEEPBREATH. The malicious C++ executable, named WAVESHAPER, is made to collect system information and distribute a Go-based downloader codenamed HYPERCALL, which is then used to serve additional payloads.
CHROMEPUSH is deployed using SUGARLOADER, a second C++ downloader.
SILENCELIFT is a simple C/C++ backdoor that transmits system data to a command-and-control (C2) server. DEEPBREATH can obtain file system access by manipulating macOS's Transparency, Consent, and Control (TCC) database. This allows it to steal data from Google Chrome, Microsoft Edge, Brave, Telegram, and the Apple Notes app, as well as iCloud Keychain credentials.
Similar to DEEPBREATH, CHROMEPUSH steals data; however, it is written in C++ and is installed as a browser extension for Google Chrome and Brave, posing as an offline editing tool for Google Docs.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)