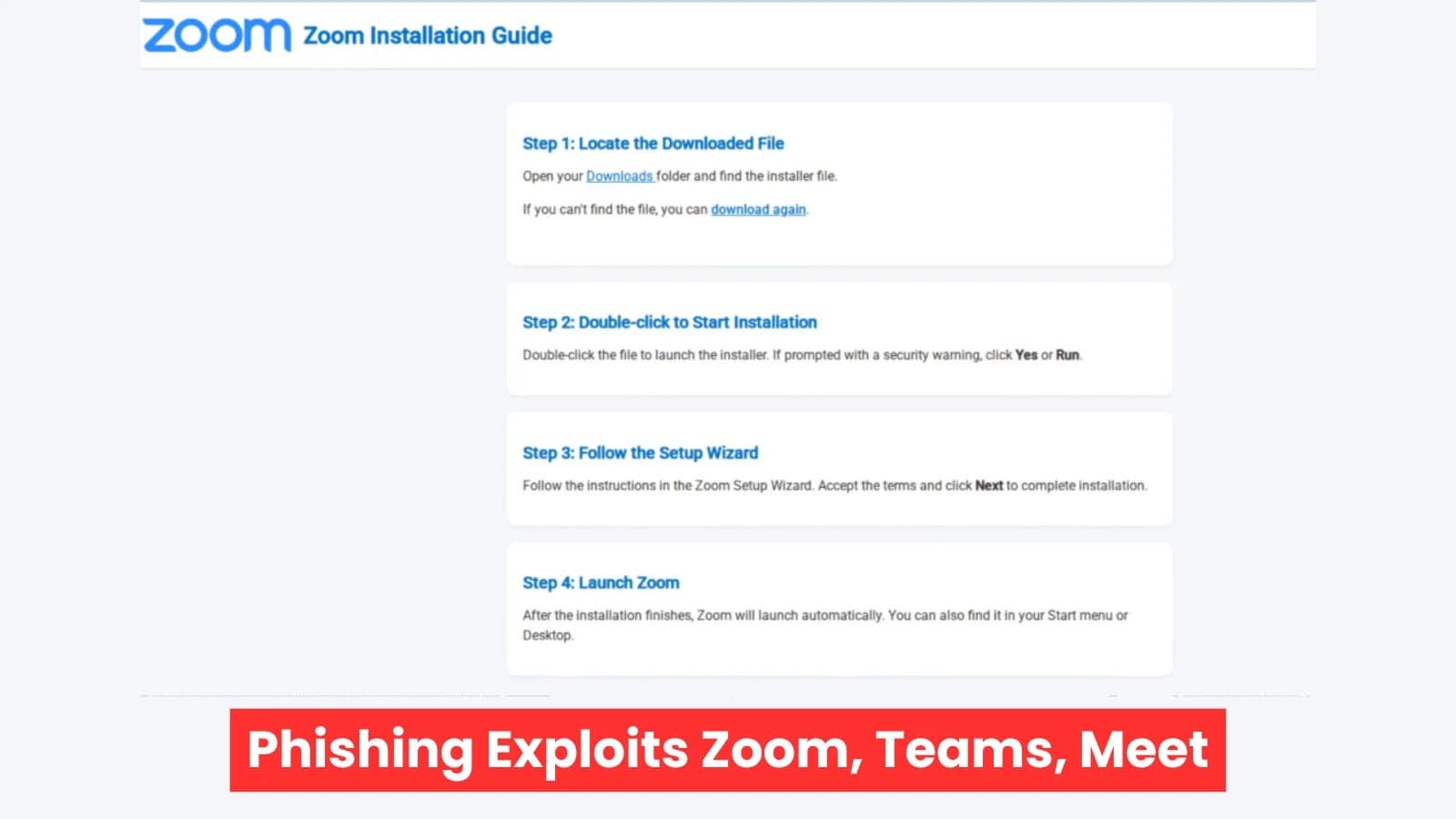
an increase in phishing attempts that take advantage of people's faith in video conferencing platforms such as Zoom, Microsoft Teams, and Google Meet. Attackers urge corporate workers to join urgent calls by sending them phony meeting invites. After clicking, victims are taken to realistic-looking spoof pages that imitate the actual apps.
These pages create a sense of authenticity and pressure to not miss out by displaying participant lists with names "joining" in real time. When users attempt to enter the call, the trap is triggered. When an app version is out-of-date or incompatible, a pop-up alert is displayed. Victims need to download and execute a "mandatory software update" in order to participate.
As a result, the payload is waiting on typo-squatted domains like zoom-meet.us.
The file, which poses as a harmless fix, takes advantage of people's hectic work schedules by encouraging them to disregard security alerts. The Hook: Inauthentic Updates Keep Dangerous Tools Hidden Attackers create pixel-perfect phishing websites that mimic the official Google Meet, Teams, and Zoom user interfaces. Victims are presented with familiar layouts that include dynamic elements, such as the addition of participants to increase urgency.
Zoom Teams Meet Phishing Exploits (Source: netskope) Then, claiming a software error, the phishing page blocks access. It provides detailed instructions on how to "update" the app, including downloading from a fake link. The file that was downloaded is not a patch. It is an MSI installer or digitally signed executable that has been renamed to blend in, such as ZoomWorkspaceinstallersetup.msi or GoogleMeet.exe.
Datto RMM, LogMeIn Unattended, and ScreenConnect are the three primary remote monitoring and management (RMM) tools that Netskope researchers found to be payloads. Valid digital signatures from reliable authorities are included with these genuine enterprise tools. Zoom Teams Meet Phishing Exploits (Source: netskope) Because IT teams have pre-approved them for remote support, they frequently get past antivirus software and even endpoint detection in corporate settings.
The RMM agent gives attackers complete administrative remote access once it is installed. Without any custom malware that could cause alarms, they are able to share control, run shells, transfer files, and view screens. Threat actors can use this foothold to covertly steal data, search networks for valuable targets, or infect endpoints with ransomware.
Because video calls are highly trusted, users circumvent security measures to prevent "missing" a meeting, making them a lethal vector. These campaigns took advantage of the post-pandemic dependence on virtual meetings, which Netskope Threat Labs monitored. Phishing emails frequently use executive names to impersonate internal invitations.
In order to create FOMO, the phony websites use timers or participant counts to encourage rapid action. Some even mimic chat messages or audio cues. Email filters designed to identify blatant spam are circumvented by the smooth redirects to malicious domains. Protect Yourself from RMM Phishing in Video Invitations Attacks that combine social engineering with legitimate technology are becoming more and more dangerous for organizations.
Users should be trained by security teams to confirm invites through contacts or direct app links rather than external downloads. Enforce stringent app allowlisting and turn on multi-factor authentication for emails.
RMM payloads can be blocked and traffic to phishing domains inspected by tools such as Netskope's cloud access security brokers. Zoom Teams Meet Phishing Exploits (Source: netskope) Endpoint security needs to advance beyond signatures. Anomalies in RMM use, such as unexpected admin access from unknown IPs, are detected by behavioral analysis.
Keep an eye out for odd outgoing connections to RMM servers. Patch management is essential for keeping video apps updated and minimizing "incompatibility" excuses. Details of the Indicator Type Source Domains: teams-update.net, zoom-meet.us (campaign examples) Threat Labs at Netskope File names ZoomWorkspaceinstallersetup and GoogleMeet.exe.Datto RMM, LogMeIn Unattended, and ScreenConnect are msi Netskope Analysis RMM Tools. Payloads Seen Threat hunters can identify infections early with the aid of these indicators.
User resilience is increased through frequent phishing scenario simulations. This campaign demonstrates how attackers use everyday tools as weapons against workers who are in a hurry.
They use signed RMM agents to gain persistent access by pretending to be updates for reliable apps.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)