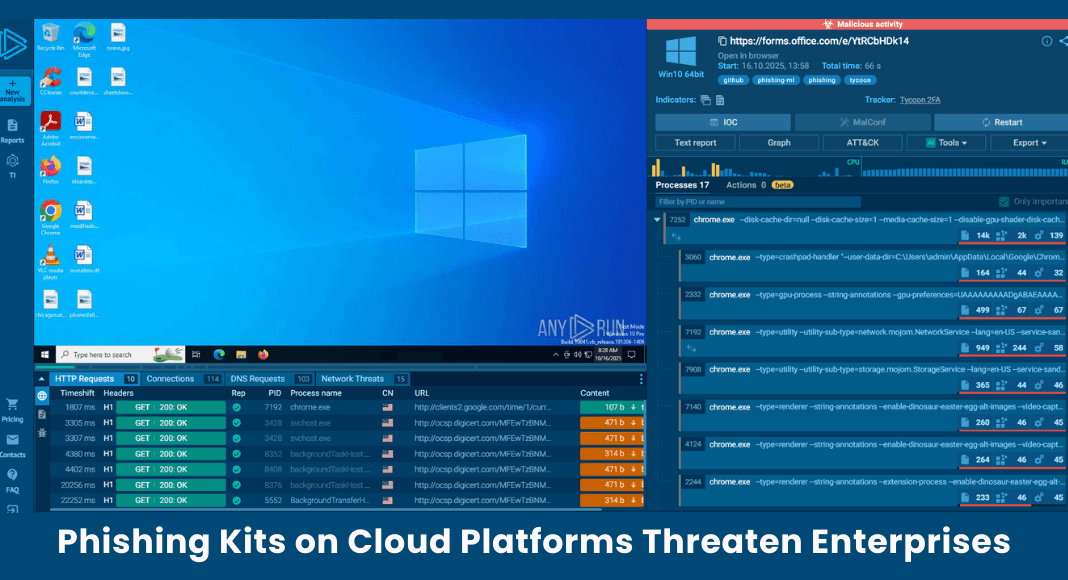
Phishing kit infrastructure is increasingly being hosted on reputable cloud and CDN platforms instead of newly registered domains, according to ANY.RUN. These campaigns pose a global threat to businesses because they frequently target enterprise users specifically. Because legitimate indicators and trusted platforms prevent malicious activity from being detected, the change poses significant visibility challenges for security teams.
Using AITM Phishing Kits for Enterprise Targeting Adversary-in-the-Middle (AiTM) kits, which assist in the execution of phishing attacks in which threat actors act as a stand-in between the victim and a legitimate service, are the driving force behind the most pervasive and hazardous phishing campaigns in existence today. The use of Browser-in-the-Browser, AiTM, and reverse-proxy techniques in modern phishing kits allows attackers to bypass multi-factor authentication (MFA), intercept live sessions, and work inside authentic login processes instead of spoofing them.
Up until recently, a common phishing attack included login forms hosted on recently registered domains, which made the malicious intent clear upon domain inspection. However, phishing threats nowadays are much more dangerous and sophisticated. Frequently, the domain name itself ceases to be a trustworthy IOC.
In order to increase the difficulty of detection, modern campaigns now host login forms on authentic AWS CloudFront, Google Firebase Storage, and Microsoft Azure Blob Storage. While the network only observes standard HTML being loaded from cloud infrastructure, victims see a "trusted" provider domain.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)