The XWorm Remote Access Trojan (RAT) is being spread by a new cyber-espionage campaign using a Microsoft Office vulnerability and well-crafted phishing emails This article explores computer xworm. . Security experts caution that the operation shows how attackers can still use vulnerabilities in legacy software to compromise contemporary systems.
XWorm is a potent Windows malware that was first discovered in 2022 and is marketed in underground and Telegram-based markets. Once installed, it gives hackers complete remote control over a victim's computer, allowing them to spy on them, steal their files, and even launch ransomware or distributed denial-of-service (DDoS) attacks. The latest campaign starts with multilingual, business-style phishing emails. Messages pose as payment confirmations, purchase orders, or shipment bank documents.
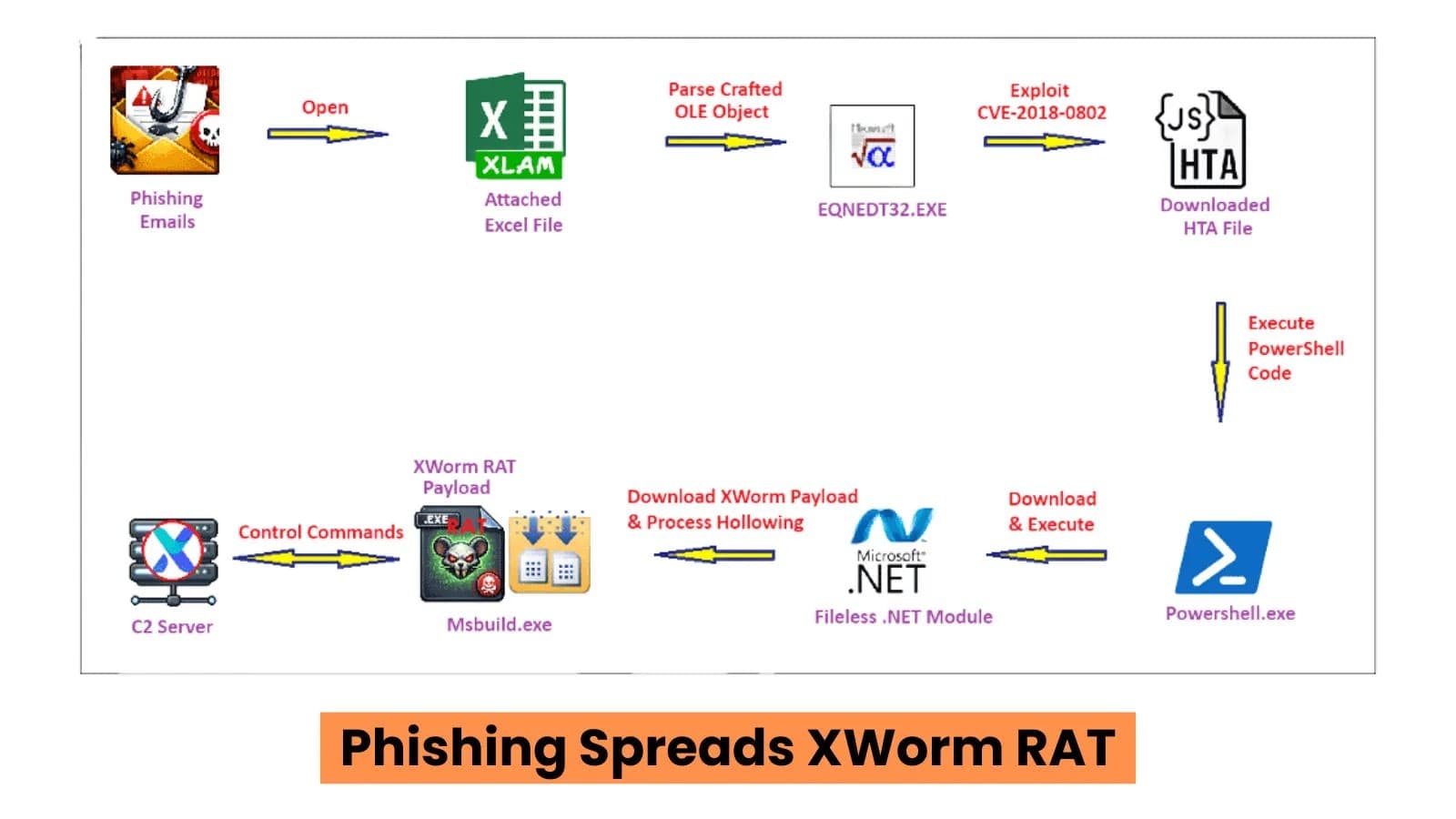
Every email encourages the recipient to review details by opening the Excel add-in file that is attached.
It is a malicious attachment. The infection chain is silently started when you open it. Excel Exploit Launches a Fileless Assault A hidden Object Linking and Embedding (OLE) component in the Excel document is intended to take advantage of Microsoft Equation Editor's remote code execution vulnerability, CVE-2018-0802.
Phishing email samples from the XWorm campaign (Source: fortinet) The vulnerable program runs embedded shellcode and processes corrupted data when the file is opened. The shellcode uses Windows utilities to launch an HTML Application (HTA) file that has been downloaded to the system. After that, PowerShell is launched by the HTA script, retrieving a disguised image file from the internet. A Base64-encoded.NET malware module is concealed within the image.
The module loads directly into memory rather than writing files to disk, which makes detection more difficult. After that, it uses process hollowing to download the completed XWorm payload and inject it into a freshly made Msbuild.exe process. This method preserves the trusted process name while inserting malicious code into the memory of the legitimate program.
This campaign's payload analysis is in line with XWorm version 7.2. CVE-2018-0802 (Source: fortinet) Remote Control, Data Theft, and Plugins is exploited by a malformed OLE object stream. Following execution, XWorm registers the compromised device and establishes a connection with its command-and-control (C2) server. The malware transmits system information, such as the operating system, antivirus software, hardware details, and username, and encrypts communications using AES.
The compromised machine can then receive commands from the attacker.
Program execution, file downloads, website opening, keystroke recording, screenshot taking, and camera or microphone control are among the capabilities. Additionally, the malware has the ability to remotely run system commands and restart or shut down the computer. XWorm's plugin architecture is one of its key features.
To increase functionality, more than 50 optional modules can be loaded from the registry. ShellExecuteExW() is used to execute the downloaded HTA file (Source: fortinet). These plugins enable credential theft, browser data harvesting, unauthorized remote desktop access, and the launching of DDoS attacks. Attackers may occasionally even use the same infection to spread ransomware.
According to researchers, the campaign draws attention to a persistent security issue: businesses frequently fail to patch outdated Office components.
Because the out-of-date executable is still present on many systems, the Equation Editor vulnerability is still actively exploited despite being years old. Security experts advise applying patches, handling unexpected attachments with caution, and shutting down legacy Office components, according to Fortinet. Within minutes, an attacker can take over a system with just one open document.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)