Pulsar RAT is a cunning malware campaign that severely damages Windows computers This article explores rat cunning malware. . It uses “living off the land” tricks tools already on your PC to stay hidden.
A batch file hidden in a user's Run registry key is the first step in the attack. This file pulls out a PowerShell loader, which then injects shellcode into legit processes like explorer.exe. It is difficult for antivirus software to detect when there are no large files on the disk. The final payload is a .NET stealer and remote access tool (RAT).
It grabs credentials, spies with webcam and mic, and sends loot via Discord or Telegram. Attackers adore its anti-detection techniques, such as looking for debuggers or virtual machines. This shows how modular .NET malware is rising, using free tools like Donut for in-memory loads.
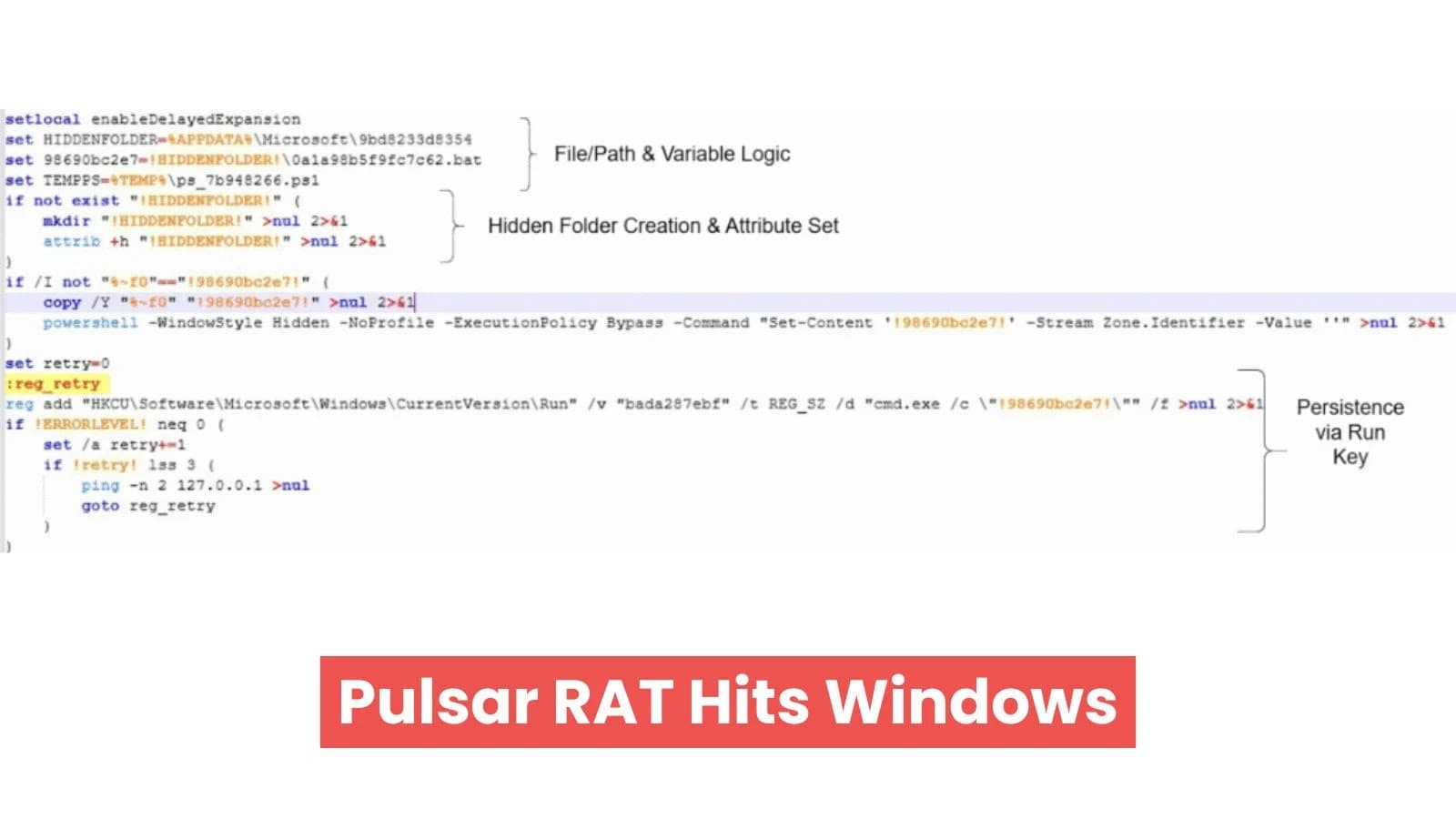
How The Attack Unfolds There are three stages in the chain. Initially, a hidden batch file creates a Run key by dropping into %APPDATA%\Microsoft[random][batfile].bat: HKCU\Software\Microsoft\Windows\CurrentVersion\Run[random] = "cmd.exe /c [bat path]." At login, it runs quietly.
Attack Flow (Source: Point Wild) The batch decodes its own Base64 blob (marked ::6bbd64163c24f552::) to a temporary PS1 file, such as ps_7b948266.ps1 in %TEMP%, and then launches it with the execution policy bypassed. Then it cleans up. PowerShell does the heavy lift: XOR-decrypts Donut shellcode, waits 80 seconds to dodge monitors, and injects into svchost.exe via CreateRemoteThread. If necessary, a watchdog loop uses APIs like VirtualAllocEx and WriteProcessMemory to respawn it in explorer.exe.
Run key persistence (Source: Point Wild) Donut decrypts (via Chaskey cipher) to Client.exe (MD5: 666493877fb7328c3e8c313fbcfdfd1e).
Pulsar is loaded by this.NET file.Stealer37.dll and Common.dll are stored in memory. Stage Key Artifacts Technique 1. Batch %APPDATA%\Microsoft\9bd8233d8354\0a1a98b5f9fc7c62.bat HKCU\Run\bada287ebf Run key 2 for persistence: PS Loader %TEMP%\ps_7b948266.ps1 XOR shellcode Watchdog and process injection 3: .NET RAT Client.exe Pulsar.Stealer37.dll and Common.dll RAT controls (remote shell, task manager disable, UAC toggle) and stealer modules are included in the Donut shellcode RAT Powers and Data Theft Pulsar RAT packs.
Anti-analysis excels: background threads pursue injections, virtual machines, and debuggers (x64dbg, dnSpy). It profiles the host, hooks clipboard for crypto wallets, snaps screens, and streams webcam/audio.
Targets of Stealer37 100+ apps: Examples of Categories Tools for Remote Use AnyDesk, TeamViewer, PuTTY FTP Clients FileZilla, WinSCP VPNs NordVPN, ExpressVPN, Chrome passwords for browsers and games, Steam messengers, Discord, and Telegram According to Point Wild, loot goes into ZIPs with IntelIX.txt summary, exfiltrated to Discord webhooks or Telegram bots. C2 hits such as 185.132.53.17:7800. T1055 (Process Injection), T1059.001 (PowerShell), T1562.001 (Disable Tools), and T1027 (Obfuscation) are mapped to MITRE ATT&CK.
PowerShell script file decoded (Source: Point Wild) Reboot to Safe Mode, scan with UltraAV (detects as Trojan_210126_Donut_Client). By observing behavior, it outperforms anti-VM techniques. MD5 Filename 648c0ba2bb1cde47fa8812f254821a72 0a1a98b5f9fc7c62.bat 69392e0d2b877cb932ab709ebe758975 ps_7b948266.ps1 666493877fb7328c3e8c313fbcfdfd1e Client.exe 0020b06dc2018cc2b5bf98945a39cbd3 Pulsar.Stealer37.dll 3abcad7678dd78832a164349aceeaa59 Common.dll This campaign combines custom code for long-term theft with public tools. Patch Windows, watch Run keys, and use behavior-based defenses.
Set Cyberpress as a Preferred Source in Google











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)