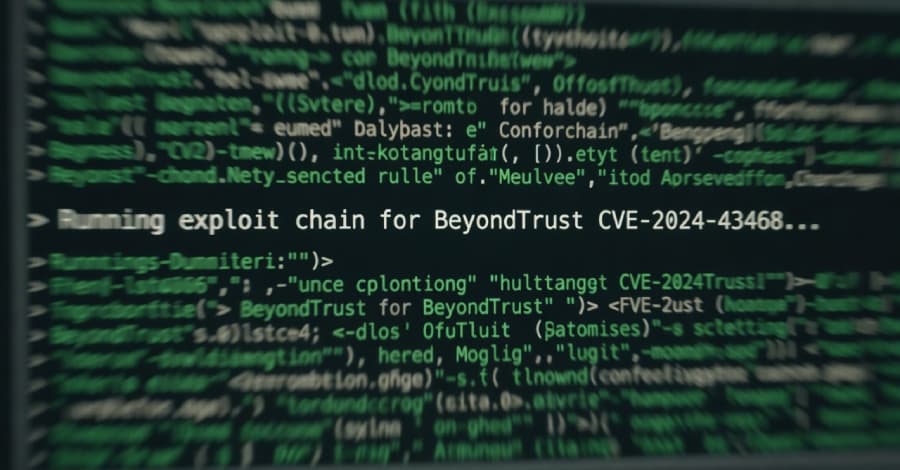
According to watchTowr, threat actors have begun to take advantage of a recently discovered serious security vulnerability affecting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products. In a post on X, Ryan Dewhurst, head of threat intelligence at watchTowr, stated, "Overnight we observed first in-the-wild exploitation of BeyondTrust across our global sensors." "Get_portal_info is being abused by attackers to extract the x-ns-company value before establishing a WebSocket channel."
CVE-2026-1731 (CVS score: 9.9) is the vulnerability in question, which could enable remote code execution by an unauthenticated attacker using specially constructed requests.
Last week, BeyondTrust pointed out that if the vulnerability is successfully exploited, an unauthenticated remote attacker may be able to run operating system commands in the context of the site user, leading to data exfiltration, unauthorized access, and service interruption. The following patches have been applied: Privileged Remote Access (Patch BT26-02-PRA, 25.1.1 and later) and Remote Support (Patch BT26-02-RS, 25.3.2 and later). The use of CVE-2026-1731 shows how quickly threat actors can turn new vulnerabilities into weapons, drastically reducing the amount of time defenders have to patch vital systems.
It has been discovered that the targeted attacks deliver Chrysalis, a backdoor that was previously unknown.
The Notepad++ update pipeline compromise is thought to have occurred over almost five months, from June to October 2025, even though the supply chain attack was completely stopped on December 2, 2025. The incident was described as precise and a "quiet, methodical intrusion" by the DomainTools Investigations (DTI) team, suggesting a clandestine intelligence-gathering mission intended to minimize operational noise. Additionally, it described the threat actor's preference for multi-year campaigns and lengthy dwell times.
The fact that the Notepad++ source code was preserved and that the malicious payloads were delivered by trojanized installers is a crucial component of the campaign.