Researchers in cybersecurity have revealed DKnife, a gateway-monitoring and adversary-in-the-middle (AitM) framework used by threat actors with a connection to China since at least 2019 This article explores cybersecurity revealed dknife. . The framework consists of seven Linux-based implants that are intended to deliver malware through routers and edge devices, perform deep packet inspection, and alter traffic.
According to the existence of exfiltration modules for well-known Chinese mobile applications like WeChat, code references to Chinese media domains, and credential harvesting phishing pages for Chinese email services, its main targets appear to be Chinese-speaking users. Ashley Shen, a researcher at Cisco Talos, wrote in a report released Thursday that "DKnife's attacks target a wide range of devices, including PCs, mobile devices, and Internet of Things (IoT) devices."
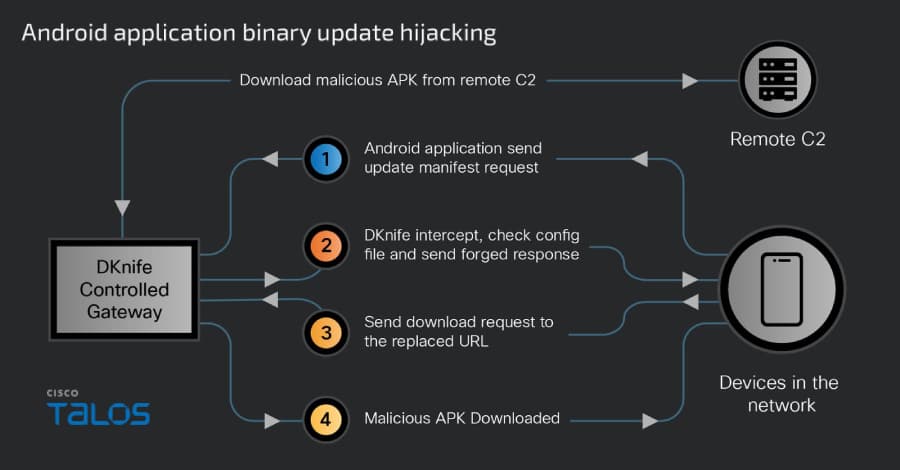
"It exploits binary downloads and Android application updates to deliver and interact with the ShadowPad and DarkNimbus backdoors." The cybersecurity firm claimed to have found DKnife while continuing to monitor another Chinese threat activity cluster codenamed Earth Minotaur, which is connected to tools such as the DarkNimbus (also known as DarkNights) backdoor and the MOONSHINE exploit kit.
"The sslmm.bin component terminates and decrypts POP3/IMAP connections, displays its own TLS certificate to clients, and examines the plaintext stream to extract usernames and passwords in order to harvest email credentials." "The 'PASSWORD' tag is applied to the extracted credentials, which are then sent to the postapi.bin component and finally sent to distant C2 servers." "dknife.bin," the framework's central component, handles deep packet inspection, enabling operators to run traffic monitoring campaigns that range from "covert monitoring of user activity to active in-line attacks that replace legitimate downloads with malicious payloads."
Serving updated C2 to DarkNimbus malware variants on Windows and Android is one example of this. utilizing IPv4 and IPv6 Domain Name System (DNS)-based hijacking to enable malevolent JD redirects.domains related to com stealing and substituting updates for Android applications related to e-commerce platforms, taxi-service platforms, gaming, pornographic video streaming apps, video streaming, image editing apps, and Chinese news media by intercepting their update manifest requests. Using pre-configured rules to hijack Windows and other binary downloads and deliver them via DLL side-loading the ShadowPad backdoor, which loads DarkNimbus and disrupts communications from PC-management and antivirus software, such as 360 Total Security and Tencent services Real-time user activity monitoring and reporting to the C2 server "Sophisticated targeted attack campaigns continue to target routers and edge devices," Talos stated.
Knowing the instruments and TTPs that threat actors use is essential as they step up their attempts to compromise this infrastructure. Modern AitM threats combine deep-packet inspection, traffic manipulation, and customized malware delivery across a variety of device types, as demonstrated by the discovery of the DKnife framework.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)