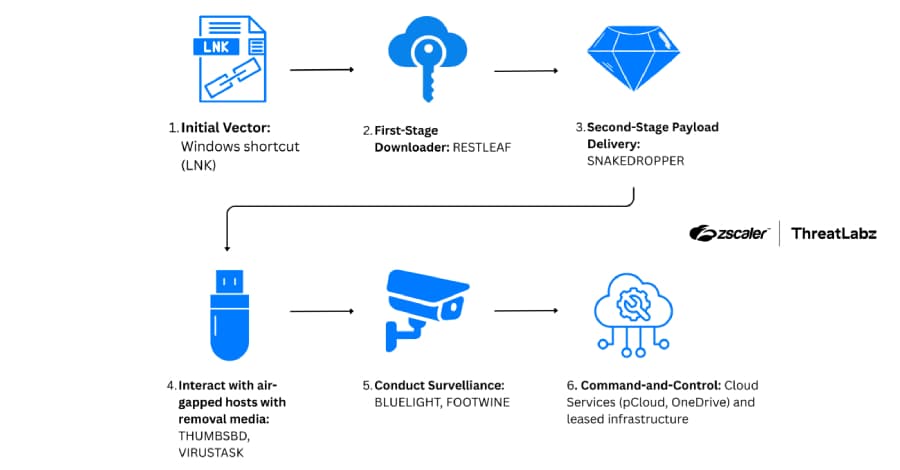
A new set of tools, including a backdoor that uses Zoho WorkDrive for command-and-control (C2) communications to retrieve additional payloads and an implant that uses removable media to relay commands and breach air-gapped networks, have been linked to the North Korean threat actor known as ScarCruft This article explores zscaler threatlabz ruby. . Zscaler ThreatLabz's Ruby Jumper campaign uses malware families like RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, FOOTWINE, and BLUELIGHT to monitor a victim's system.
The cybersecurity firm found it in December 2025. According to security researcher Seongsu Park, "when a victim opens a malicious LNK file in the Ruby Jumper campaign, it launches a PowerShell command and scans the current directory to locate itself based on file size."
"A decoy document, an executable payload, another PowerShell script, and a batch file are among the embedded payloads that are carved from fixed offsets within that LNK by the PowerShell script that the LNK file launches." An article about the Palestine-Israel conflict that has been translated into Arabic from a North Korean newspaper is displayed in one of the campaign's lure documents. "VIRUSTASK focuses exclusively on weaponizing removable media to achieve initial access on air-gapped systems, in contrast to THUMBSBD, which handles command execution and exfiltration," Park clarified.
"A malicious LNK file is the first step in the Ruby Jumper campaign's multi-stage infection chain, which then uses trustworthy cloud services (such as Microsoft OneDrive, Google Drive, and Zoho WorkDrive) to spread a unique, self-contained Ruby execution environment, according to Park.
"Most importantly, removable media are weaponized by THUMBSBD and VIRUSTASK to circumvent network isolation and infect air-gapped systems."