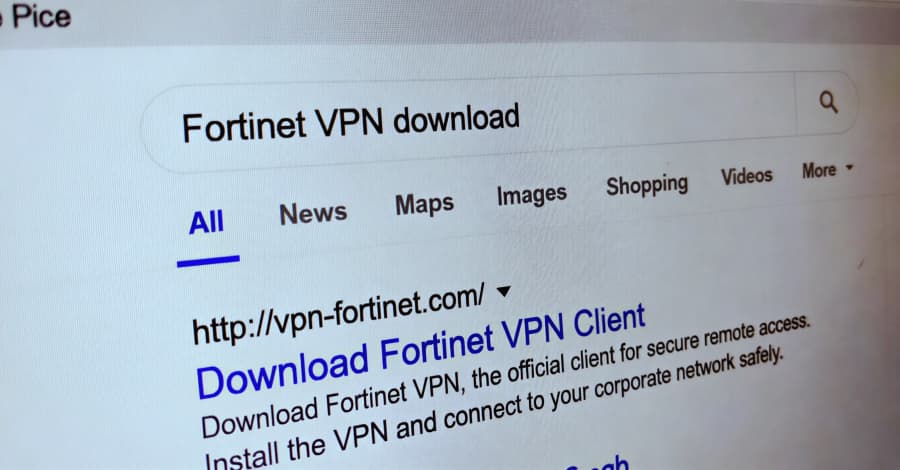
Microsoft has shared information about a credential theft campaign that uses fake virtual private network (VPN) clients that are spread through search engine optimization (SEO) poisoning methods. "The campaign sends people looking for real enterprise software to malicious ZIP files on attacker-controlled websites to install digitally signed trojans that pretend to be trusted VPN clients while stealing VPN credentials," said the Microsoft Threat Intelligence and Microsoft Defender Experts teams. The Windows maker saw the activity in mid-January 2026 and linked it to Storm-2561, a threat activity cluster that has been spreading malware through SEO poisoning and pretending to be well-known software vendors since May 2025.
Cyjax was the first to record the threat actor's campaigns. They showed how SEO poisoning was used to send people looking for software from companies like SonicWall, Hanwha Vision, and Pulse Secure (now Ivanti Secure Access) on Bing to fake sites and trick them into downloading MSI installers that install the Bumblebee loader. In October 2025, Zscaler revealed a new version of the attack.
People saw the campaign using fake websites ("ivanti-vpn[. ]org") to spread a trojanized Ivanti Pulse Secure VPN client to people who were looking for real software on Bing. The fake websites stole the victim's VPN credentials from their computer.
Microsoft said that this shows how hackers use trust in search engine rankings and software branding as a way to trick people into giving them their data when they are looking for enterprise VPN software. It makes things worse that trusted sites like GitHub are being used to host the installer files. The GitHub repository has a ZIP file with an MSI installer file inside that pretends to be real VPN software but installs harmful DLL files at the same time.
As before, the main goal is to use a version of an information stealer called Hyrax to get VPN credentials and send them to someone else. To get the user's credentials, a fake but convincing VPN sign-in dialog is shown.
After the victim enters the information, they get an error message telling them to download the real VPN client this time. Sometimes, they are sent to the real VPN website. The Windows RunOnce registry key is used by the malware to make sure it runs again after every system restart.
Microsoft said, "This campaign has traits that are similar to financially motivated cybercrime operations used by Storm-2561." "Taiyuan Lihua Near Information Technology Co., Ltd." has digitally signed the bad parts. The tech giant has since removed the GitHub repositories that the attacker controlled and canceled the real certificate to stop the operation.
To protect against these kinds of threats, organizations and users should use multi-factor authentication (MFA) on all accounts, be careful when downloading software from websites, and make sure that the software is real.