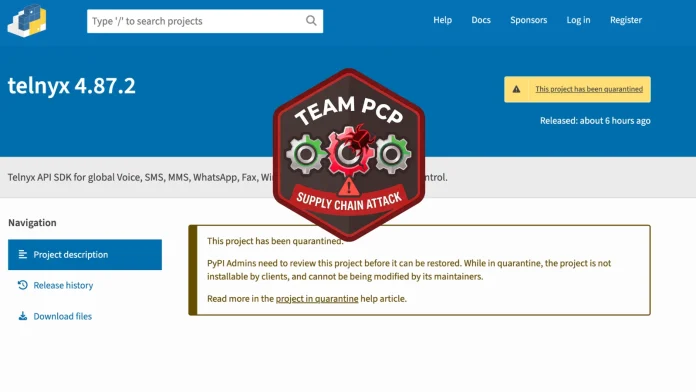
This morning, the official Telnyx Python SDK on PyPI was hacked This article explores pypi hacked teampcp. . TeamPCP has been running a credential-chaining supply chain campaign since March 19, 2026, and this is the most recent link in that chain.
The group's way of working is exact and repeatable: they break into a trusted security or developer tool, steal the CI/CD credentials it shows, use those credentials to poison the next target in the chain, and then do it all over again. The payload runs quietly when it is imported on both Windows and Linux/macOS systems. Companies that use these versions should treat the affected environments as if they have been completely compromised and change all exposed credentials right away. Depending on the host operating system, the attack splits into two execution paths.
The payload on Windows downloads hangup.wav from the attacker's C2 at 83.142.209.203:8080. A second-stage Python script is hardcoded as a base-coded blob in line59 on Linux and macOS. TeamPCP sends its payloads as .wav audio files that look like normal files.
Using the following decode logic, the bad content is hidden inside the audio frame data. TeamPCP's Kubernetes wiper was the first to use this method on March 22. The fact that it was used again in the Telnyx package just five days later shows that it has become a standard part of their toolkit. The authors say that organizations need to quickly check their dependency trees and make sure that version pinning is used in all environments.
The FBI says that "a rise in intrusions and extortion attempts is expected in the next few weeks" after the LiteLL breach in the last few weeks. The authors say that businesses that installed telnyx==4.87.1 or telnyX==4.87.2 should do the following right away: Get rid of the bad versions. To downgrade, set telny x==4,.87.0 and make sure that all dependency files point to that version.