GootLoader, a JavaScript (also known as JScript) malware loader, has been seen to use a corrupted ZIP file that is intended to evade detection by concatenating between 500 and 1,000 archives This article explores javascript malware gootloader. . As a result, many automated workflows are unable to analyze the contents of the file because the archive cannot be processed by programs like WinRAR or 7-Zip.
Simultaneously, the default Windows unarchiver can open it, making it possible for victims of the social engineering scheme to extract and execute the JavaScript malware. GootLoader is usually disseminated through malvertising or search engine optimization (SEO) poisoning techniques, directing users seeking legitimate templates to hacked WordPress websites that contain malicious ZIP files.
It is intended to deliver secondary payloads, such as ransomware, just like other loaders. Since at least 2020, the malware has been found in the wild. Malware campaigns spreading the malware reappeared in late October 2025 using new techniques, such as using custom WOFF2 fonts with glyph substitution to obfuscate filenames and taking advantage of the WordPress comment endpoint ("/wp-comments-post.php") to deliver the ZIP payloads when a user clicks a "Download" button on the website.
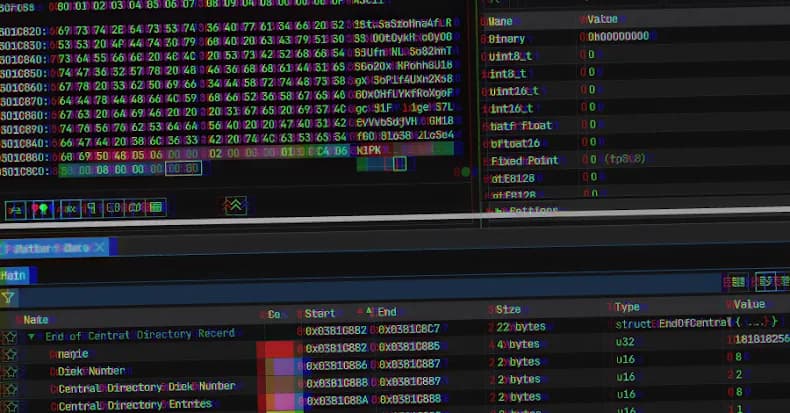
According to Expel's most recent research, threat actors are using increasingly complex obfuscation techniques to avoid detection, such as concatenating 500–1,000 archives to create a malicious ZIP file. Truncate the end of central directory (EOCD) record in the archive so that it omits two crucial bytes from the expected structure, resulting in parsing errors. Unarchiving tools will anticipate a sequence of nonexistent ZIP archives if non-critical fields like disk number and number of disks are randomized.
"The randomized values in certain fields and the random number of files concatenated together are a defense-evasion technique called 'hashbusting,'" Walton clarified.
It is pointless to search for that hash in other environments because each user who downloads a ZIP file from GootLoader's infrastructure will actually receive a unique ZIP file. Hashbusting is used by the GootLoader developer for both the JScript file and the ZIP archive. In order to circumvent security measures intended to identify the transmission of a ZIP file, the attack chain basically entails delivering the ZIP archive as an XOR-encoded blob that is decoded and repeatedly appended to itself on the client-side (i.e., on the victim's browser) until it reaches a predetermined size.
When the victim double-clicks the downloaded ZIP archive, Windows' built-in unarchiver opens the ZIP folder with the JavaScript payload in File Explorer. Since the contents of the JavaScript file were not specifically extracted, launching it causes it to be executed via "wscript.exe" from a temporary folder. After establishing persistence by creating a Windows shortcut (LNK) file in the Startup folder, the JavaScript malware uses cscript to execute a second JavaScript file that generates PowerShell commands to advance the infection.
The PowerShell script is used in earlier GootLoader attacks to gather system data and obtain commands from a distant server.
Organizations are advised to use a Group Policy Object (GPO) to guarantee that JavaScript files are opened in Notepad by default rather than being executed via "wscript.exe" in order to counter the threat posed by GootLoader. They should also think about preventing "wscript.exe" and "cscript.exe" from executing downloaded content if it is not necessary.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)