TA584, a popular initial access broker (IAB), has been exposed by researchers for intensifying attacks in late 2025 This article explores targeting campaign ta584. . This threat actor, which has been monitored since 2020, tripled the volume of its campaigns between March and December, switching to ClickFix social engineering and introducing Tsundere Bot, a new piece of malware.
TA584, which overlaps with Microsoft's Storm-0900, uses high-velocity email campaigns that avoid static detections to target organizations worldwide. Changing Strategies and Quick Iteration The 2025 operations of TA584 represent a departure from predictable trends. Early campaigns used geofenced URLs or macro-enabled Excel to deliver payloads like Ursnif, reusing infrastructure for months. Now, campaigns launch, modify, and retire in hours or days, cycling lures, branding, and landing pages.
This churn counters defenses, with emails from hundreds of compromised senders or ESPs like SendGrid.
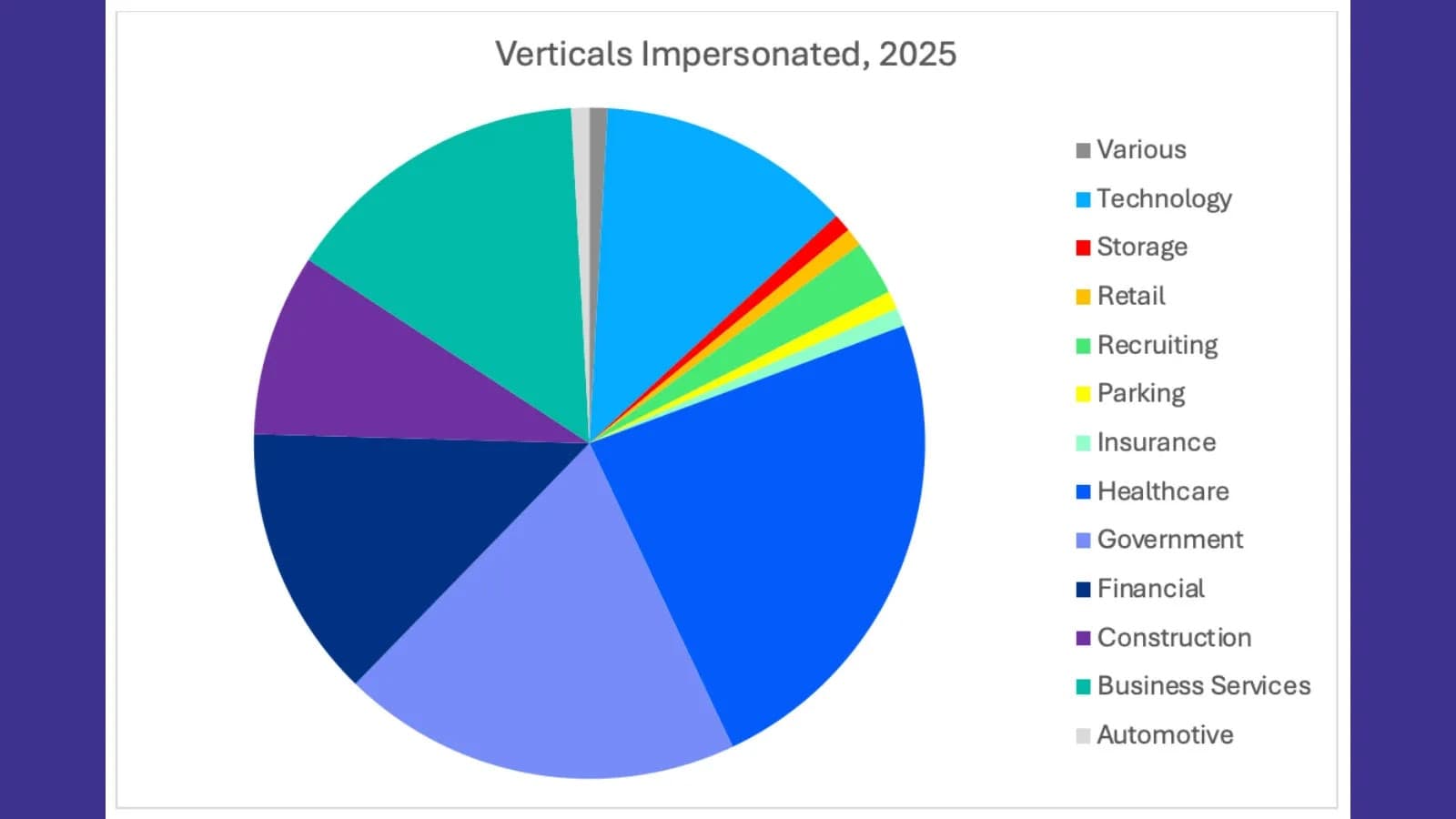
Healthcare (hospitals, Medicare), government (OSHA, HSE), and services (PayPal, BBB) are all impersonated by lures. Themes include medical results, tax notices, debt collection, and rarely seen personalized package photos. Throughout 2025, operational tempo increased (Source: Proofpoint).
Brands are frequently localized for areas like North America, the UK, Germany, and Australia, and they rotate quickly. Clicks like "Review this now" or "Resolve your issue" are motivated by urgency. Attack chains begin with distinct, geofenced URLs that lead to landing pages that are protected by CAPTCHA. Since July 2025, ClickFix dialogs have been used to trick users into pasting PowerShell commands using Windows+R by posing as error popups.
Chains include IP filtering on actor-controlled hosts (e.g., 94.159.113.37 since April), AWS S3 buckets, and TDS such as 404 TDS for redirects.
Tsundere Bot: A Novel MaaS Loader Appears Tsundere Bot and XWorm "P0WER" were first released by TA584 on November 28, 2025. Installing Node.js is necessary for this backdoor, which is sold as Malware-as-a-Service (MaaS) through "Tsundere Netto/Reborn" panels. System profiling (CPU/GPU, locale), WebSocket C2, arbitrary JS execution, SOCKS5 proxying, and autotasks are among the capabilities.
According to Proofpoint, ClickFix initiates a PowerShell loader that retrieves an intermediary script. Installing Node.js from nodejs.org, it connects via EtherHiding and queries Ethereum blockchain RPCs for C2 (e.g., 193.17.183.126:3001) or hardcoded fallbacks after decrypting AES-encrypted Node.js files (loader + bot). It pings C2 for commands and aborts on CIS locales (Russian, Ukrainian). TA584's use indicates a ransomware risk; Kaspersky associates it with RMM drops and phony game installers.
XWorm "P0WER" endures through dynamic remote fetches, hollowing into RegSvcs.exe, and SharpHide (null-byte registry hiding). Both avoid detection through fileless execution and AMSI bypass. Worldwide Attribution and Targeting Every campaign, TA584 opportunistically sends thousands of emails across verticals.
A purported image of actual mail (Source: Proofpoint) North America is the dominant region, but in the summer of 2025, Germany experienced a surge in Europe, with a rotational focus using language-matched lures. It is highly likely connected to Russian cybercrime through artifacts and malware.
94.159.113.37 TA584 Host (AS216234) April 2025 85.236.25.119 Tsundere Bot C2 December 9, 2025 80.64.19.148 XWorm C2 November 10, 2025 85.208.84.208 XWorm C2 September 9, 2025 178.16.52.242 XWorm C2 October 28, 2025 bbedc389af45857f4724. Keep an eye on powershell.exe creating node.exe. The innovation of TA584 highlights the flexibility of IAB.
Anticipate new payloads and European expansion in 2026; maintain your lead with behavioral defenses.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)