KnowBe4 Threat Labs has uncovered a sophisticated phishing campaign hitting North American businesses and professionals. Attackers are using the OAuth 2.0 Device Authorization Grant flow to compromise Microsoft 365 accounts, which include Outlook, Teams, and OneDrive. By avoiding Multi-Factor Authentication (MFA) and strong passwords, this technique provides long-term access to company data.
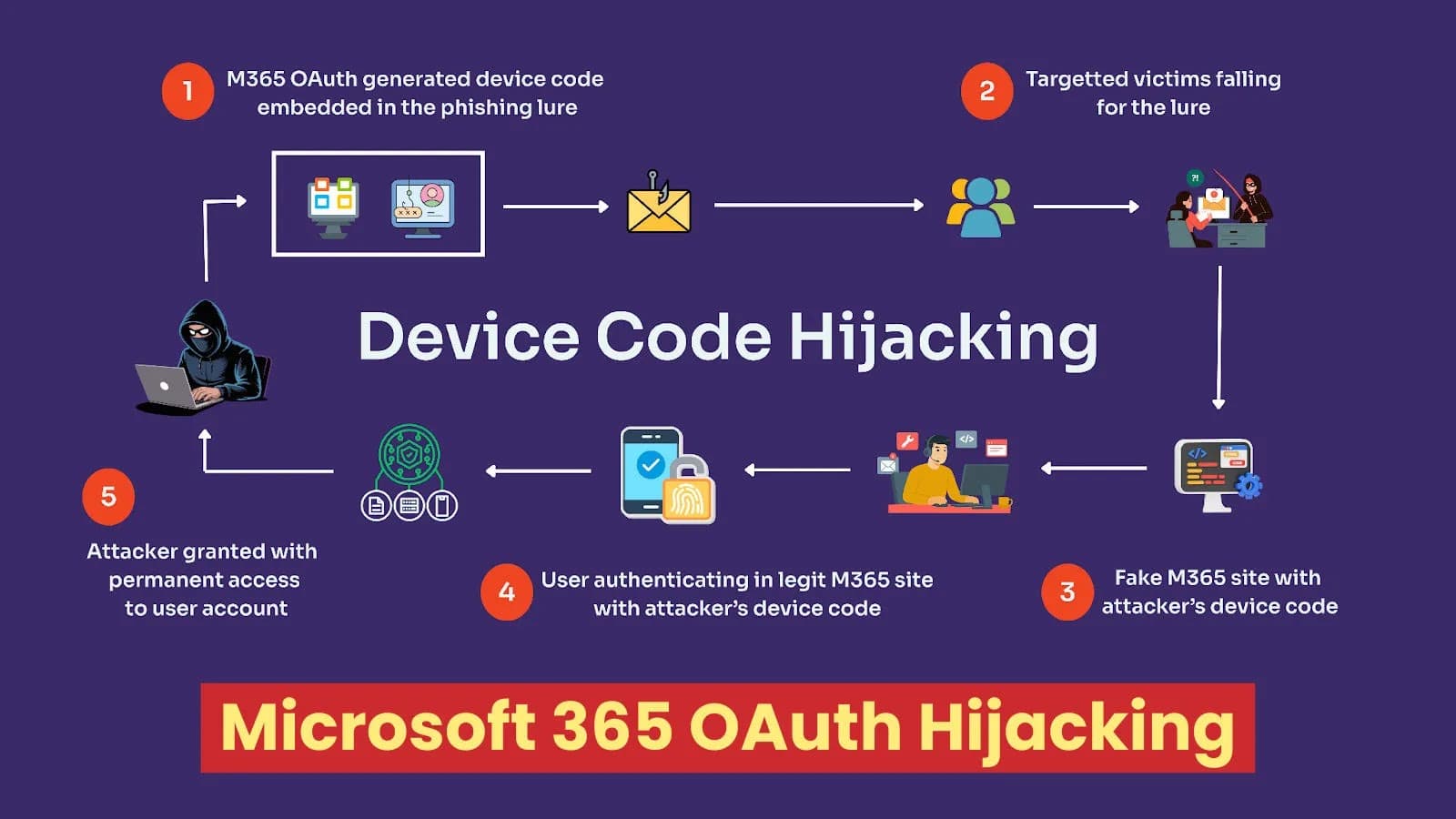
With more than 44% of victims in the US, the operation, which was first discovered in December 2025, targets the tech, manufacturing, and financial sectors. Complete read/write/send access to files, calendars, email, and even administrative tasks is made possible by stolen OAuth access and refresh tokens. There are five stages to the attack. It starts with attackers registering a malicious OAuth app in Microsoft 365 to generate a unique device code, delivered via targeted phishing emails.
After clicking on malicious links, victims are taken to pages controlled by the attacker that imitate Microsoft services. This forces them to enter the code at the official microsoft.com/devicelogin portal. Microsoft issues legitimate tokens that attackers can poll and take over in real time for long-term access after authenticating with credentials and MFA.
This gets around conventional defenses because only authentic tokens from the actual domain are stolen, not credentials. An illustration of a landing page under attacker control and user authentication (Source: knowbe4) Complex Attractions and Practical Effects In order to hook victims, attackers use urgent social engineering. Despite security training, common strategies entice clicks by posing as reliable services or offering financial incentives.
An illustration of a compromised OAuth token found in the attacker's C2C (Source: knowbe4) Example of a Lure Type Subject Line Strategy/Hook False Payment Confirmation EFT REF-UIVJRW Verification: Notice of Distribution Processing of Payment Transferring $125,000 USD urgently within a window of one to two days False Document Sharing [Name of Contact] distributed the "Q4 Profit related Salary Bonus Distributions Form – Year 25" document. poses as a Google Drive share with an enticing salary bonus Voicemail Notification [External Email] Voicemail (925 seconds) Interest in the unusually lengthy phony voicemail The campaign's success is fueled by these lures, which are found in devices like PhishER Plus consoles. After capturing tokens, attackers continue to have covert access and steal confidential information without setting off standard alarms.
This persistence poses serious risks to security teams.
Compromised tokens can be used for data theft, ransomware preparation, or espionage because they avoid MFA checks and remain active until they are revoked. Real-world phishing lure examples in the PhishER Plus console (Source: knowbe4) Increased incidents are reported by North American companies in the targeted sectors, highlighting the necessity of prompt searches in email and sign-in logs. As stated in Indicators Of Compromise and Mitigation Steps, use these artifacts to hunt and block.
Examples of IOC Types Noreply-application-integration@google.com is the sender address. logon.sharefileselfservices is a malicious domain.cloud, newcrowdcapital.com, and sso-services.com URLs for Cloud Storage: storage.cloud.google.com/…/check.html, storage.cloud.google.com/…/captcha.html Subject: Patterns Voicemail (### seconds), ####### Verification: Payment for Distribution Notice Completed, #### Distributed document: "Q4 Profit related Salary Bonus Distributions Form Year 25"











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)