APT36, a cyber espionage group with ties to Pakistan, Transparent Tribe, has increased the scope of its attacks to include cybersecurity companies and India's growing startup scene This article explores apt36 cyber espionage. . In a report published in February 2026, the Acronis Threat Research Unit (TRU) described this campaign in detail, pointing out that the Crimson RAT malware was distributed through customized phishing.
Since 2013, Transparent Tribe has focused on South Asian countries, including Afghanistan and India. To spy on officials and organizations, the group usually employs social engineering lures that are themed around government, defense, education, and military events. It frequently drops remote access trojans like Crimson RAT or GymRAT and uses straightforward payloads like malicious LNK files, ISO containers, HTA scripts, and ZIP archives. This new activity is a departure, targeting cybersecurity and open-source intelligence (OSINT) startups.
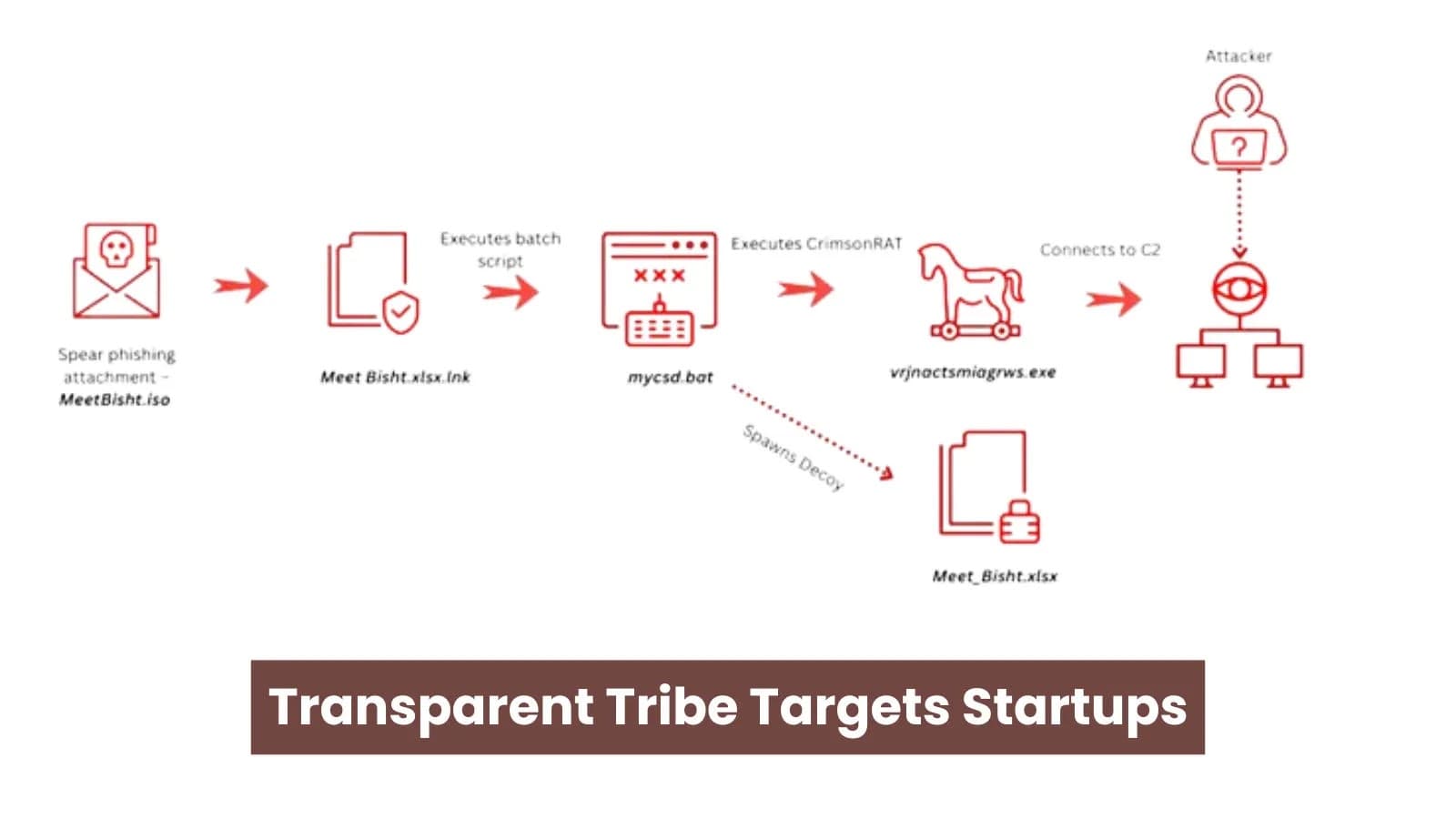
Because the malware, infrastructure, and tactics match those of previous campaigns since October 2025, TRU confidently attributes it to Transparent Tribe. To establish credibility, spear-phishing emails with ISO files like "MeetBisht.iso," which are named after startup founders, are used at the beginning of campaigns. When the ISO is opened, the Crimson RAT payload is hidden as "excel.exe," along with a phony Excel shortcut ("Meet Bisht.xlsx.lnk"), a decoy document, and a batch runner script ("mycsd.bat").
The LNK uses a minimized command prompt to launch the batch file, displaying the decoy as it copies files to C:\ProgramData\ and %APPDATA%. It runs the RAT covertly after using PowerShell to remove Mark's Web flags, avoiding SmartScreen.
The malicious container-based payload's contents (Source: acronis) Decoys make reference to legitimate startups such as Voldebug, which provides OSINT tools for use by SIS law enforcement. This implies that attackers look for information on companies supporting the security initiatives of the Indian government. Crimson RAT Dissection Crimson RAT is a 34MB bloated.NET trojan that is padded with junk data to get around analysis limits and scanners.
Its small (80–150KB) core code is concealed by obfuscated strings, random names, and a unique TCP protocol over hardcoded C&C servers like 93.127.133.9:443. Decoy-extracted displays information about Voldebug's director (Source: acronis). The RAT obtains network data, usernames, AV information, and system information. Screen recording, webcam streaming, microphone audio capture, file searches, transfers, deletions, process killing, and command execution are all made possible by it.
The LNK file's properties (Source: acronis) Ability An explanation of surveillance Webcam, microphone recording, and screen capture File Operations: List drives, search, upload, download, and remove files User rights, security software, and the OS version of System Recon Process Control List, terminate, and execute commands and tools Attribution and Infrastructure C&C connections to the past Tribe operations are transparent, including domain certstorein.shop used in GymRAT government attacks. Filename pivots, such as "Evidence.pdf.lnk" (which misspells "Evidence"), point to additional lures. A sample of code pertaining to screen capture capabilities (Source: Acronis) VirusTotal samples uploaded from India exhibit consistent TTPs.
It is blocked by Acronis EDR/XDR. IoC Type Value Description ISO 5c4488b4eda72d245dac5382f3587f09 MeetBisht.iso LNK 4976ef0054b0283c0d013be2f442e17b Malicious shortcut RAT 5b4a48815446cd40d8e141cbf8582296 Crimson RAT (Excel.exe) Batch 22218f19425b78dfd6a4f42e43f5486f Runner script C&C IP 93.127.133.9 Main server This pivot highlights startups as fresh espionage prizes, given their government ties.
Defenders should block listed IoCs, scan ISO/LNK files, and keep an eye on odd batch or PowerShell activity. By reusing their tools, Transparent Tribe demonstrates evolution rather than reinvention, which calls for caution in India's tech industry.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)