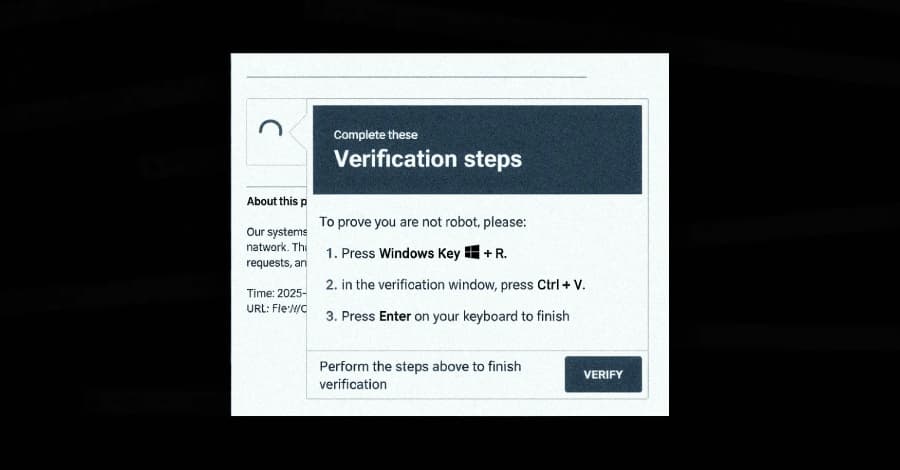
A new campaign has used the ClickFix social engineering trick to spread a malware loader that had not been seen before. The loader, on the other hand, has been found to hide what it really does by assigning meaningless variables. It seems that the goal is to use multi-purpose malware that can do bad things all over the cyber kill chain and avoid being detected by security controls.
G DATA also talked about a new malware loader called Kiss Loader that is sent out through phishing emails with Windows Internet Shortcut files (URLs) attached to them.
The malware can tell when removable media devices, like USB drives, are plugged in and copy files that have malware in them. These files are called "Chrome setup" and "Firefox installer.lnk." It also installs a bad browser extension that steals login information as it is entered on login pages and stays on the computer even after the user logs out.
The loader decrypts and runs Venom RAT, which is a type of AsyncRAT, in the last step using APC injection. We don't know how common attacks using Kiss Loader are right now, or if it's being sold as malware-as-a-service (MaaS). That being said, the person behind the loader says they are from Malawi, and it's not clear if they are offering it as a service.
Right now, a small number of computers in the U.S. and Europe are testing the loader. It's not clear yet if it will be available in other countries or as a separate product in the future. The malware is still in its early stages.
Security experts don't think it's a threat actor, but they do think it's based in Malawi.